On Tuesday, February 25, 2020, the California Court of Appeal added another opinion to its growing body of case law on claims made and reported issues, holding that there is no coverage under a claims-made employment practices liability policy for a claim that was not timely reported when it was first made in an administrative proceeding, and that the insurer need not show it was prejudiced to deny coverage on that ground. The Court’s decision affirmed the judgment of the Los Angeles County Superior Court sustaining the demurrer of Greenwich Insurance Company and XL Insurance America Inc (XL).
In 2018, Troutman Sanders obtained a judgment in favor of XL after the trial court sustained its demurrer, without leave to amend. The trial court held that Charges of Discrimination filed with the Department of Fair Employment and Housing (DFEH Charge) were Claims, as that term was defined under the employment practices liability policy. Because the policy provided claims-made coverage, the insured was required to report the DFEH Charge to the program administrator identified in the declarations “as soon as practicable” but no later than 60 days after the expiration of the policy period. Even though the insured reported the DFEH Charge to its insurance broker within the policy period, the trial court held that such notice did not satisfy the reporting requirements of the policy, which required notice to the insurer’s program administrator. The insured’s failure to provide timely notice of the DFEH Charge precluded coverage for both the DFEH Charge and the subsequent civil complaint filed against the insured, as the trial court also held that the insured’s subsequent tender of the civil complaint to the program administrator, after the end of the policy period, was untimely.
On appeal, the insured argued that the trial court erred in sustaining the demurrer because the insured sufficiently alleged that its tender was timely, and even if it was not, the insurer could not deny coverage for the Claim without demonstrating prejudice. In a 19-page unpublished opinion, the Court of Appeal affirmed the judgment in full. The opinion touched upon several heavily litigated areas of insurance law, including whether an administrative charge constitutes a claim under an employment practices liability policy (here, it was), whether an insured’s broker may be deemed to be an agent of notice for an insurer (not in this case), and whether the notice-prejudice rule applies to claims-made coverage (not in California). The Troutman Sanders team consisted of Jennifer Mathis and Jenni Katzer.
The opinion is available on Westlaw as AHSL Enters. v. Greenwich Ins. Co., No. B292484, 2020 WL 897259 (Cal. Ct. App. Feb. 25, 2020) and on Lexis as AHSL Enters. v. Greenwich Ins. Co., No. B292484, 2020 Cal. App. Unpub. LEXIS 1279 (Feb. 25, 2020).
Lenders should view as cautionary tales two recently handed down decisions regarding UCC-1 financing statements and the perfection of security interests. On December 20, 2019, the U.S. Bankruptcy Court for the District of Kansas in In re Preston held that security interests in personal property were unperfected because the UCC-1 incorrectly set forth the debtor’s name. On January 2, 2020, the U.S. Bankruptcy Court for the Western District of North Carolina in In re Jarvis held that a parent company’s filing of a UCC-1 did not perfect the security interest of its wholly owned subsidiary. The results of these cases show the importance of diligence and attention to state law requirements in filing UCC-1s.
In re Preston
Background
In In re Preston, Dewey Dennis Preston, the debtor, entered into two separate retail installment sale and security agreements to finance his purchase of two pieces of farm equipment. The agreements were entered into with CNH Industrial Capital of America, LLC on June 26, 2015 and January 5, 2016, respectively. Following the execution of these financing agreements, CNH filed UCC-1s to perfect its liens on each purchase. Preston’s name was set forth as “Preston” in the box for surname and “D.Dennis” (with a period and no space) in the box for first name. Preston’s driver’s license listed his name as “Preston D Dennis.” Preston filed for bankruptcy under Chapter 12 on October 3, 2018.
Preston treated CNH’s claim as unsecured, to which CNH objected. CNH argued its filing of the UCC-1s perfected its interest, giving CNH priority over any subsequent claims on the assets. Article 9 of the Kansas Uniform Commercial Code requires financing statements to bear the debtor’s name exactly as it is listed on his or her driver’s license. Article 9 addresses the potential for errors on a financing statement, and directs that financing statements are effective, even with a minor error or omission, as long as the error or omission does not make the statement “seriously misleading,” and further that a statement that fails to list the debtor’s name exactly as it appears on his or her driver’s license is “seriously misleading.” Preston asserted that the discrepancy in name on the UCC-1s was “seriously misleading” and that the financing statements were necessarily ineffective.
Analysis
The sole issue before the court was whether CNH’s UCC-1s were effective in perfecting its security interests. The Bankruptcy Court for the District of Kansas determined they were not. CNH did not list Preston’s name in the strict manner required by Article 9, so the interests were unperfected. There is a “safe harbor” exception to this exacting requirement, which provides that a financing statement will not be considered seriously misleading, even with error, if a simple search of the debtor’s correct name, using the filing office’s standard search logic, would find it. Neither of the two searches conducted located CNH’s financing statements.
The court relied on official commentary from the 2010 revision of the UCC, which stated that the name should be exactly the same as it is on the debtor’s driver’s license, even if the name indicated on the license contains an error. The commentary further provided that, in the case of ambiguity or doubt, the party filing the financing statement may choose to file under a number of names for the debtor, which CNH did not do.
Outcome
CNH’s financing statements were held to be seriously misleading because they did not conform to the debtor’s driver’s license, nor were they saved by the “safe harbor” exception. As a result, they were ineffective in perfecting CNH’s security interests. Accordingly, Preston’s treatment of the CNH claim as unsecured was proper.
In re Jarvis
Background
In In re Jarvis, the debtor, Jacob D. Jarvis, obtained a loan from Strategic Funding Source, Inc. on October 6, 2015. The parties entered into a security agreement in connection with the loan, in which Jarvis granted Strategic a security interest in his assets. Strategic, through its representative, Corporation Services Company (CSC), filed a UCC-1 to perfect its security interest. The secured party representative services agreement between CSC and Strategic listed Strategic as the customer, not any of its affiliates. The financing statement listed CSC as the secured party and did not make reference to any affiliates of Strategic. Jarvis repaid the Strategic loan in February 2016.
On February 20, 2018, Jarvis obtained two additional loans from a subsidiary of Strategic, Money Works Direct, Inc. The parties entered into separate security agreements, in which Jarvis granted Money Works a security interest in his assets. Money Works did not file a financing statement to perfect its interest. Strategic did not amend its initial financing statement to include Money Works as a secured party nor did it assign its initial financing statement to Money Works.
In March 2019, Jarvis filed for bankruptcy under Chapter 13, and listed Money Works as holding an unsecured claim against the estate. The servicing provider for Strategic responded with a proof of claim, alleging it held a secured claim on behalf of Strategic.
Analysis
Strategic argued that it was unnecessary for Money Works to file a financing statement because Strategic and Money Works are part of the same investment syndicate, with Strategic as lead syndicator and Money Works as its wholly owned subsidiary and affiliate. Strategic invested the funds involved in the 2015 and 2018 transactions with Jarvis. Strategic claimed that the secured parties were therefore the same and that Strategic was the secured party under the Money Works transactions. Strategic argued that it acted both on its own behalf and as a representative of Money Works when it filed the UCC-1, so the Money Works security interests were perfected as a result of that UCC-1.
Strategic also argued that language in the Money Works security agreements supported its argument because the language references obligations owed to Money Works and its affiliates: “to secure [the Debtor’s] payment and performance to [Money Works] and its affiliates or the Funders, . . . [the Debtor] hereby grants to [Money Works] a security interest in all personal property of [the Debtor].” The court rejected this argument because the granting of a security interest was only to Money Works, and did not explicitly include affiliates.
In support of this rejection, the court cited In re Adirondack Timber Enterprise, Inc., 2010 WL 1741378 (Bankr. N.D.N.Y. Apr. 28, 2010), which stated a security agreement executed solely between a debtor and their creditor does not grant security interests in the collateral to an affiliate of the creditor.
Outcome
The court held that Strategic did not receive security interests by virtue of the security agreements between Money Works and Jarvis, and further that Strategic’s financing statements were not capable of perfecting Money Works’ security interests because the security agreements explicitly granted security interests to Money Works alone. Thus, Jarvis’s objection was sustained and the court’s treatment of the claim as unsecured was deemed proper. Although Money Works pursued many lines of argument, it was unsuccessful in its attempt to convince the court to allow it to rely on an earlier filed UCC-1 in favor of its parent company to perfect its security interests.
What Can Lenders Take Away From These Decisions?
The court in In re Preston held that security interests in personal property were unperfected due to the lender’s misstatement of the debtor’s name on their UCC-1s. This case, specifically, highlights the importance of properly indicating the debtor’s name, consistent with the relevant state law. Particular attention may also be required where the debtor is a natural person. Lenders should look to controlling state law and UCC provisions to make sure they are in conformity with the required procedure and other various specifications. As the court in In re Preston discussed, when in doubt, lenders may want to consider submitting more than one financing statement or listing more than one version of the debtor’s name.
The court in In re Jarvis held that a party’s security interests were not perfected by their parent company’s filing of a UCC-1. Even where there appears to be an affiliation or relationship of some sort, such as parent-subsidiary as in this case, security interests are only granted to the named party and will not flow to affiliates solely by virtue of their relationship. The secured party should file its own UCC-1, and not rely on the UCC-1s of its affiliates.
The lenders in both cases made preventable errors. The result is that they were unable to perfect their interests and were left with unsecured claims. These cases illustrate the importance of diligence in completing and submitting UCC-1s when seeking to perfect security interests. It is important to check the pertinent provisions of the UCC and other relevant state law requirements. The ability of a lender to secure its claim may come down to a mere period.
Melissa Griest, an intern in the Corporate and Securities Practice Group, assisted with the research and drafting of this article. She is not admitted to practice law.
On January 30, 2020, the Board of Governors of the Federal Reserve System (the Board) issued its final rule for determining whether a company has control over a bank or other company for purposes of the Bank Holding Company Act (the BHCA) and the Home Owners’ Loan Act (the HOLA), and the control presumptions promulgated under Regulation Y and Regulation LL, respectively (collectively, the Control Rule).[1] The Control Rule becomes effective April 1, 2020. The Control Rule provides specific guidance in place of the Board’s decades-long, ad hoc approach to control evaluations and creates a useable and easy-to-understand tiered framework. Following up on our client alert from May 2019, this article summarizes the key points from the Board’s Control Rule and its implications for financial institution holding companies and their investors.
The Control Rule and the Tiered Framework
The Control Rule provides increased predictability and simplicity to control determinations by the Board and clarifies how combinations of investment and influence will, and will not, subject investors to Board supervision and regulation. Community banks and other financial institutions that rely on substantial investments from a few significant investors to raise capital will be affected the most by the Board’s Control Rule. At the same time, because control determinations can lead to federal supervision of non-bank business relationships, the Control Rule also has the potential to disincentivize certain bank investment in entities such as fintech companies.
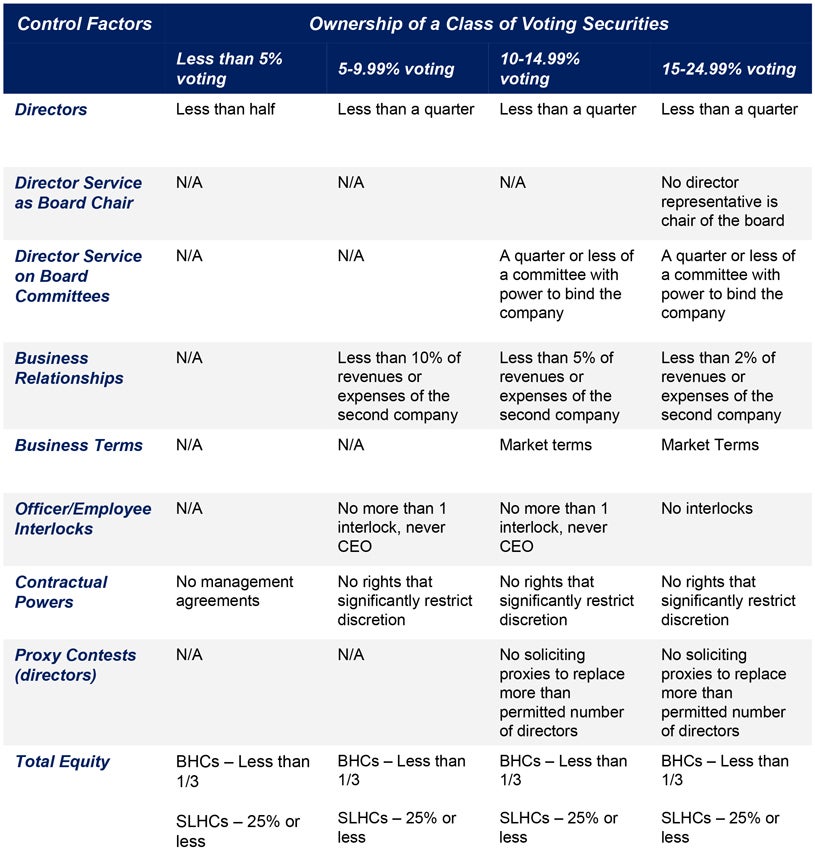
The Control Rule is closely aligned with the April 2019 rulemaking proposal, as it retains the initially proposed tiered framework (see below), which incorporates a series of presumptions of control based on ownership of a class of voting securities.[2] The framework works as a matrix – a company may be presumed to be in control of a target second company based on five levels of ownership of voting securities in that target second company: less than five percent, five percent, ten percent, 15 percent, and 25 percent, with the presumption triggered at levels below 25 percent, if any of nine types of relationships exists and exceeds the threshold on the table applicable to the ownership level. The matrix is as follows:
By working through the tiered framework, investors and holding companies can determine what level of investment to pursue depending on how comfortable they are with a potential control determination. Of course, triggering a presumption of control does not mean that the investor is deemed to control the company for purposes of the BHCA or HOLA. As with control determinations prior to enactment of the Control Rule, a presumption of control may be rebutted. In connection with the Control Rule, the Board has also raised the prospect that standard-form passivity commitments will no longer be used (discussed in more detail below).
Directors and Proxy Contests
The Board’s Control Rule permits an investor holding more than five percent but less than 25 percent of voting securities in a target company may appoint up to a quarter of the directors serving on the board of the target company. More importantly, investors holding less than five percent of the voting securities in a target company may appoint up to half of the directorships on the target board.[3]
The Board’s Control Rule also significantly lessens the restrictions on the roles of directors representing noncontrolling interests. For example, an investor holding less than ten percent of the voting securities of a target company is free from restrictions on service as the board chair or on key committees. The Control Rule also expands the ability of noncontrolling investors to propose director nominees and conduct proxy solicitations.[4] However, these abilities are limited as the percentage of voting securities held by the investor in the target company increases.
Total Equity of Noncontrolling Investments
The Board’s Control Rule permits a company to own up to one-third of the total equity of a second target company that is a bank holding company (BHC) and have that investment remain noncontrolling. This is reflected in the bottom row of the tiered framework.[5]
With respect to a savings and loan holding company (SLHC), the Board’s Control Rule takes into account the differences with respect to the definition of “control” under the BHCA and HOLA. For example, under HOLA, a person controls a SLHC if the person has more than 25 percent of any class of voting securities of the SLHC (as opposed to 25 percent or more of any class of voting securities of a BHC under the BHCA).[6] Based on this and other differences between the BHCA and HOLA, the Board’s Control Rule imposes a lower total equity percentage – 25 percent or less – for presumption of noncontrol of a SLHC.
Furthermore, the Control Rule retains the Board’s proposed total equity calculation methodology, which is keyed to the amount of the target company’s shareholders’ equity (calculated according to U.S. GAAP) that is allocated to the stock held by the investor. The Board believes that the U.S. GAAP-based core methodology of the Control Rule is effective, fit for purpose, well-understood, and easy to apply for investors and holding companies. Interestingly, the Control Rule includes (without change) a provision whereby debt or other interests may be treated as equity if the interests are functionally equivalent to equity. However, according to the preamble, the Board expects to reclassify debt as equity under the rule only under unusual circumstances to prevent evasion of the rule.
Business Relationships
In its initial proposal, the Board proposed that where a company’s business relationships with a target second company exceed the applicable percentage of either the investor’s or the target company’s revenues or expenses, a presumption of control would arise. However, as reflected in the tiered framework above, in connection with the Control Rule the Board determined that only the revenues and expenses of the target second company, and not the investor’s, are relevant when calculating the triggering revenue percentage threshold.[7] This gives welcome breathing room to investors and target holding companies who have established business relationships. Nevertheless, the Board emphasized that a relationship between two companies may raise supervisory or other concerns whether or not the relationship raises controlling influence concerns.[8]
Passivity Commitments
In its proposed rulemaking, the Board gave no mention to passivity commitments. However, in the final pages of the preamble to the Control Rule, the Board announced that it does not intend to obtain standard-form passivity commitments going forward in the ordinary course. Moreover, while passivity commitments may be requested in specific contexts (e.g., ESOPs, mutual fund complexes, etc.), the Board has invited companies currently subject to standard passivity commitments to contact the Federal Reserve to seek relief from these commitments. Absent unusual circumstances, the Board expects to be receptive to such requests for relief. Now appears to be the opportune time for investors and holding companies subject to standard passivity commitments to seek relief.
No Grandfathering or Transition Period
While several commenters asked the Board to apply the new control framework only prospectively, others suggested grandfathering for existing investments or a delayed phase-in period. However, because the Board views the Control Rule to be generally consistent with its current practice, the Board determined that it would not grandfather existing structures and would not provide a transition period for firms to conform existing investments.[9] Further, the Board does not expect to review investment structures that have already been reviewed by the Federal Reserve unless they were materially altered from the facts and circumstances of the original review. Accordingly, holding companies and investors should be aware that the Control Rule becomes effective as of April 1, 2020.
Conclusion
The Board’s Control Rule is a significant development for financial institutions with direct ramifications for investors, investment companies, and holding companies, as well as their respective business relationships and management, operational and policy decisions. The impact of the Board’s new framework will likely be felt for many years to come – including years in which banks and their holding companies may need to seek equity investment in times of stress. We recommend that all financial institutions and bank investors review and carefully weigh the implications of the Board’s Control Rule – particularly those relying on the Board’s 2008 policy statement on equity investments as more favorable terms and conditions may be available from the Board following implementation of the Control Rule.
[1] See Board of Governors of Federal Reserve System, Press Release – Federal Reserve finalizes rule to simplify and increase the transparency of the Board’s rules for determining control of a banking organization (Jan. 30, 2020), available here.
[2] Id. at Appendix – Summary of Tiered Presumptions (reproduced herein).
[3] See id. at section II.B. (pp. 19-23).
[4] See id. at section II.B. (p. 38).
[5] See also id. at section II.B. (pp.36-37) and section III.D. (pp. 69-73).
[6] For further discussion of the Board’s rationale for the distinction between total equity holdings of a BHC and SLHC, please refer to section IV of the preamble to the Board’s final rule (pp. 83-85).
[7] Id. at section II.B. (pp. 26-27).
[8] Id. at section I.B. (p. 8 n.21).
[9] However, the Board did state that, to the extent that a company previously considered an existing relationship between two companies to not constitute control, the relationship was not reviewed by the Federal Reserve, and the relationship would be presumed to be a controlling relationship under the final rule, company may contact the Board or its staff to discuss potential actions. See id. at section V. (pp. 86-87).
On January 9, 2020, the United States Court of Appeals for the Eleventh Circuit issued its decision in Williams v. First Advantage Lns Screening Solutions, a case watched closely by the background screening industry. In Williams, the Court affirmed a $250,000 compensatory damages award and reduced a $3.3 million punitive damages award to $1 million in an individual mixed-file claim brought pursuant to 15 U.S.C. § 1681e(b) of the Fair Credit Reporting Act (FCRA). The decision addressed a basic legal requirement in the background screening industry: connecting background information to common names. The matching procedures involved in Williams are similar to those recently scrutinized by the CFPB in another notable FCRA action that we highlighted in the Southern District of New York. In that action, the CFPB also addressed procedures in attributing public records to persons with common names when other definitive unique identifiers, particularly a Social Security number, are absent, coming to similar conclusions as the Williams court.
Background
In Williams v. First Advantage, Plaintiff Richard Williams sued Defendant First Advantage for alleged violations of the FCRA in connection with twice attributing the criminal background information of another individual to Plaintiff. In two criminal background reports developed a year apart, Defendant reported to Plaintiff’s potential employers criminal background information related to a “Ricky Williams.”
In its description of the background of the case, the Williams Court focused heavily on Defendant’s procedures for connecting criminal background information with individuals with common names. In order to attribute criminal background information to an individual with a similar name, Defendant’s employees preparing the report were required to attempt to locate three identifiers, such as name, date of birth, Social Security number, or a driver’s license number. Where the employee was unable to locate a third identifier, he or she must note that they were unable to do so and obtain approval by a supervisor prior to releasing the report. Evidence at trial showed that in both instances, Defendant’s employees preparing Williams’s reports relied on only two identifiers.
Further, Plaintiff disputed the criminal information contained in the first report, which was later removed. However, different criminal background information related to “Ricky Williams” appeared on Plaintiff’s second criminal background report developed a year later. Importantly, the employees who developed the second report lacked access to information pertaining to the disputed criminal history in the first.
At trial, Plaintiff argued that he suffered lost wages of $78,272 and suffered additional emotional and reputational harm as a result of the reporting. The jury found Defendant willfully failed to follow procedures to assure the maximum accuracy of the information in Plaintiff’s consumer report, as required by § 1681e(b) of the FCRA. The jury awarded Plaintiff $250,000 in compensatory damages and an astonishing $3.3 million in punitive damages. After the trial court entered judgment in favor of Plaintiff, Defendant filed a motion for judgment as a matter of law, which the trial court subsequently denied. Defendant appealed.
Decision
Defendant raised three arguments on appeal. The first two arguments related to its motion for judgment as a matter of law. First, it argued that the jury’s award of $250,000 should be vacated because the Plaintiff failed to show reputational harm. Second, it argued that Plaintiff had failed to establish a willful violation of the FCRA. Third, Defendant argued that the $3.3 million punitive damages award was unconstitutional under the Due Process Clause.
In a brief analysis, the Court affirmed the district court’s denial of Defendant’s motion for judgment as a matter of law with respect to Plaintiff’s showing of reputational harm and willfulness under the FCRA. The Court’s analysis with respect to willfulness is particularly notable, considering the extent to which Defendant’s procedures were scrutinized. The Court recognized that despite having a policy requiring use of a third identifier for screenings involving common names absent supervisor approval for use of two, evidence in the case indicated this did not occur in common practice. Defendant’s Vice President of Operations stated at trial that locating a third identifier was “king of aspirational.” The Court understood this to infer that Defendant consciously disregarded a known risk of violating the FCRA. The Court further pointed out Defendant failed to follow its own procedure during the preparation of both reports related to Plaintiff. Finally, the Court looked to Defendant’s lack of a procedure for flagging disputed criminal background information to avoid repeat occurrences. It found this evidence sufficient to support a willful violation of the FCRA.
The Court spent the majority of its seventy-seven-page opinion analyzing the constitutionality of the jury’s $3.3 million punitive damages award. The ratio of punitive damages to compensatory damages in Williams was 13:1. The Court noted the Supreme Court has previously found an award of punitive damages with a 4:1 ratio is “close to the line” of unconstitutionality, and an award that exceeds a single-digit ratio is likely a violation of the Due Process Clause. However, after a lengthy review of relevant case law, the Court determined in candor that it is “ultimately up to the reviewing court to eyeball the punitive damages award and, after weighing the egregiousness of the particular misconduct and the harm it caused, decide whether the award is grossly excessive.”
In the end, the Court ruled that a 4:1 ratio was appropriate in this case and reduced the jury’s punitive damages award to $1 million based on the amount of compensatory damages awarded and its assessment of the reprehensibility of Defendant’s conduct. The Court’s reprehensibility analysis focused primarily on Defendant’s use of only two identifiers when attributing the criminal history of Ricky Williams to Plaintiff, as well as its failure to flag this information once alerted to its inaccuracy to avoid future mispairing.
Based on two concurring opinions filed with the majority decision, the $1 million award was a compromise by the three-judge panel. One judge on the panel would have affirmed the $3.3 million award, while another opined that $500,000 was the proper figure. As one of the judges noted, “[t]he only way to resolve such a disagreement is to meet in the middle—as we have done.”
In its punitive damages analysis, the Court noted the tension between competing analyses of Defendant’s error rate with respect to mispairing individuals with criminal background history and the extent to which this placed Defendant on notice of its conduct. Based on evidence at trial, the national rate for all errors in reporting raised through Defendant’s dispute resolution process between 2010 and 2013 was .38%—less than one half of one percent. In mitigating the alleged reprehensibility of its conduct, Defendant argued that this figure was rather low.
Plaintiff, on the other hand, argued that based on the high number of reports issued by Defendant, errors still affected some 13,000 individuals. Importantly, however, Plaintiff did not show the extent to which those 13,000 individuals had similar experiences to the Plaintiff. The Court concluded that the extent to which the Court could determine that Defendant was on notice was limited because Plaintiff “failed to bore down into the numbers.” Indeed, the court expressly stated that a high frequency of related experiences would be something the “Plaintiff should have seized on and proved at trial if he wanted to justify an award of extraordinarily high punitive damages.”
The decision comes on the heels of a Complaint filed by the CFPB against Sterling Infosystems, Inc. in the United States District Court for the Southern District of New York alleging violations under the FCRA and a simultaneously filed Proposed Stipulated Final Judgment and Order. In the Complaint, the CFPB appeared to stake out a position that matching a criminal record to an individual with a common name based solely on a first and last name and date of birth was inadequate.
Challenges to matching procedures utilized by the background screening industry continue to be an area of focus in FCRA litigation. The Eleventh Circuit’s Williams decision represents a noteworthy development on that front.
Download the publication here.
One of the most negotiated and fundamental provisions in any contract is the manner in which the parties will allocate risk. Also known as an “indemnity” or an “indemnification provision,” these provisions are not commonly included in a business term sheet or letter of intent. While indemnification provisions can be technically challenging and easy to gloss over, it is essential to understand what they mean so they can be appropriately and clearly drafted, the correct insurance can be purchased, and, if an incident does arise, the liable party can be easily determined.
Indemnities show up in a wide variety of contracts, and there are various reasons why a party may be willing to indemnify another — among them is in exchange for a right, good or service (e.g., to be permitted to use another’s property), as consideration for a loan or mortgage, or as a settlement of an existing dispute. This article outlines the main factors that should be considered in reviewing an indemnification provision.
Building Blocks of an Indemnification Clause
Typical indemnification provisions will be long sentences with many clauses, legal-sounding words, and long lists of specific details. The best manner to review a long-winded indemnification provision is to break it down into its component parts, which are generally as follows:
-
The Indemnitor: This is the person or entity taking on the risk or obligation. Typically, the indemnitor must be a party to the agreement but may be a guarantor or a related party. When considering the party taking on the obligation, attention should be given to whether that party has sufficient financial resources to cover the losses imposed and, if the indemnitor is an entity, whether it will continue in existence for the period of the obligation. If the indemnitor may not be able to cover the indemnity obligation, a third-party guarantor may be brought in or provisions can be added to require the indemnitor to carry insurance to cover the indemnified risk. If a third party will be taking on an indemnification obligation or guaranty, that party will have to sign on to the contract to acknowledge the obligation or sign and deliver a separate guaranty document.
-
The Indemnitee: The indemnitee is the beneficiary of the indemnification. It is important to include related parties within the definition of the indemnitee, including employees, members, partners, agents and any other party that may be related to the indemnitee and involved with the performance of the contract and all such parties’ successors and assigns.
-
Covered Damages: The damages covered by an indemnification provision should be tailored for the circumstance. In some cases, indemnification provisions will only cover claims for damages to third parties. In other cases, damages directly to the indemnitee will also be covered. Often damages must “arise out of” or “relate to” a specific place, occurrence or action, such as “all damages arising out of a breach of this agreement, or the negligence of the indemnitor.”
-
Standard of Care: Indemnification provisions can vary with regard to the standard of care exercised by the parties before an indemnification obligation will arise.
-
No Standard: In some cases, the indemnification obligation will be absolute. This often happens in a leasing situation, where the tenant is obligated to indemnify the landlord for all damages occurring within the premises, regardless of the cause or the negligence of the landlord.
-
Negligence Standard: This will mean that the indemnitor is not obligated to take on the obligation unless it has been negligent. Some contracts will also negate the indemnification language if the indemnitee is found to have been negligent as well.
-
Gross Negligence or Willful Misconduct: This is a higher bar to the indemnitor’s obligation, requiring indemnification only when the indemnitor has been grossly negligent or willfully caused a harm. Conversely, the gross negligence or willful misconduct of the indemnitee will generally relieve the indemnitor of its obligation. Depending on the state, indemnification clauses where the indemnitor takes on responsibility for the indemnitee’s gross negligence or willful misconduct may be void as a matter of law. In addition, many states do not differentiate between gross negligence and negligence, so it is important to follow state law when making these distinctions.
-
-
Specific Circumstances. Depending on the nature of the contract, indemnity provisions may include specific indemnifications related to the use of intellectual property, hazardous materials and other matters related to the circumstances of the transaction.
Insurance Implications and Other Contractual Matters
When a risk is shifted from one party to another, it is essential to determine whether the burdens are consistent with the insurance being purchased by that party and whether it makes economic sense. It can therefore be extremely helpful to have the insurance agents for both sides involved from the beginning of the negotiations, so that both parties understand whether they have sufficient coverage and the cost of that coverage. This can also help to shift the conversation away from a more emotionally charged one about who may be “in the wrong” to one about the economics of making sure that a casualty event is properly covered regardless of the cause.
For example, in a lease setting, landlords often require tenants to cover all of the risk of loss for injuries occurring within the leased premises and for damages to their personal property, even if those injuries or damages are caused by the landlord’s negligence. While at first glance this may seem draconian, the provision accomplishes two things. First, it places the burden of insuring everything within the leased premises on the tenant and relieves this burden from the landlord. Second, it means that there should not be a dispute over liability if damages or injuries occur within the leased premises; the tenant’s insurance should simply pay the claim regardless of whose negligence caused the damage. In these situations, the tenant should require the landlord to indemnify it for injuries and damages occurring in the remainder of the building (exclusive of the leased premises) and the surrounding property. In this way, the tenant should not have to insure the rest of the property that it does not control.
If the goal is to divide the insurance responsibilities between the parties regardless of the negligent party in the matter, it is also essential to obtain waivers of subrogation so that the insurer does not then try to collect from the indemnified party that may have been negligent.
In addition to the insurance provisions, special attention should be paid to any other contract provisions that shift liability or otherwise handle risk allocation. This will include provisions addressing fire or other casualty damages. These provisions should follow the indemnification and insurance obligations by not focusing on fault and instead focusing on insuring the loss and obtaining the appropriate coverage.
Other Technical Elements of an Indemnification Provision
Indemnification provisions can include additional details that will structure what will happen if an event triggers the indemnification obligations. Some examples are as follows:
-
Baskets and caps: These provisions will require a dollar threshold before an indemnification obligation is triggered and a cap on the amount of damages. These are most often seen in corporate transactions, where the purchasing party is expected to take on some risk and the selling party is not willing to retain an unlimited risk.
-
Survival periods: In many situations, the indemnification provision will last longer than the contracting period because certain damages may not be known before the expiration of the contract. However, the indemnitor may want to close the door to its obligations before the expiration of the applicable statute of limitations, so a shorter survival period for the indemnification obligations can be specified.
-
Limitation on types of damages: Indemnification provisions may limit the types of damages covered. For example, they may exclude consequential and punitive damages.
-
Choice of attorneys: Some indemnification provisions will detail which party controls the choice of counsel and the manner in which the litigation is handled. In these cases, it is essential that the party paying the claim have control over the ultimate settlement.
Takeaway
Indemnification provisions can often be a last-minute, back-and-forth item pushed by counsel for both parties and often not fully understood by clients. It is therefore vital to break down the component parts of the provisions to understand and explain the burdens and benefits early on in the process. Bringing in the insurance carrier will also quickly clarify the coverage obligations and associated costs related to any additional liability taken on in an indemnification clause. The outcome of these negotiations often rests on the relative bargaining power of the parties. If obtaining an indemnification will be vital to a particular contract, negotiating the terms upfront with the other business conditions will go a long way toward achieving the desired result.
The material in this publication was created as of the date set forth above and is based on laws, court decisions, administrative rulings and congressional materials that existed at that time, and should not be construed as legal advice or legal opinions on specific facts. The information in this publication is not intended to create, and the transmission and receipt of it does not constitute, a lawyer-client relationship.
Letters of intent (LOIs) are frequently used by parties to formalize terms for commercial real estate leases. LOIs are implemented in the beginning stages of a transaction to ensure there is a meeting of the minds on major deal issues. This article outlines steps for drafting LOIs to both protect the parties and to effectively negotiate and finalize a commercial real estate lease agreement.
The Basics
LOIs can be referred to as term sheets, memoranda of understanding, commitments or other titles, depending on the industry and business of the parties involved. Regardless of the name, an LOI is the document that sets forth the material terms and business agreement of a commercial real estate lease.
Parties and Property
An LOI should include fundamental items of a deal, including the parties and the property. An LOI must specifically state the complete legal names of the parties involved in the transaction, as well as the property address and the property type, whether warehouse, office, industrial or retail. The property description should also include any notable items such as whether the property is part of a shopping center or condominium regime, if the location is single-tenant or multitenant, or if the premises are located on a multiple parcel development.
Rental Structure, Deposits and Incentives
An LOI should clearly state the economic terms of a lease. With respect to rent, an LOI must note the base rental amount and yearly escalations, if any, as well as whether the lease is (1) a triple net (with all taxes, insurance costs and common area and operational expenses passing through and being paid by the tenant); (2) gross (with the tenant paying one monthly base rent payment and all taxes, insurance costs and common area and operational expenses built into that base rent amount); or (3) modified gross structure (being a combination of triple net and gross lease structures, with the tenant paying a monthly base rent payment and some, but not all, property expenses).
The LOI should also detail the monetary amount of any deposits, the form of the deposit (whether cash or letter of credit), and any potential reduction of the security that may be permitted by the landlord during the lease term. Further, an LOI should include any incentives, such as tenant improvement allowances and rental abatements.
Dates and Term
An LOI should include pertinent dates applicable to a lease, such as the date the premises will be delivered to the tenant, the commencement date and the rent commencement date. In addition, an LOI should identify the length of the term and any extension terms. It is best practice to also include the notice time period required to exercise an option, as well as the rental rates for an extension term in an LOI.
Elementary but Essential
Although the above noted items are rudimentary, addressing these items in the beginning stages of a transaction not only permits a party to best understand the deal but also allows attorneys to highlight and address potential issues before drafting and negotiating the lease.
For example, when representing a landlord, it is important to identify the actual tenant entity that will be party to the lease and to confirm with the landlord that the financial statements provided for the tenant match that entity name exactly. In the same light, knowing property-specific information ignites a conversation about exclusivity restrictions, operational and development regulations, and other due diligence items that may be applicable to a certain site.
Further, a client needs to understand when the premises will be delivered for its use and occupancy, as well as any potential risks arising from a delivery date that is contingent on certain work being completed at the premises. Therefore, discussing the lease commencement with a client opens discussions on issues such as the termination of an existing lease, the timing for relocating to a new location, and remedies for a landlord failing to timely deliver premises.
Client and Property-Specific Provisions
In addition to the basic elements noted above, an LOI should include all material operational and property matters that a client may require in connection with a proposed lease.
For example, parking, signage and security requirements, if any, should be negotiated and addressed in the letter. An LOI should also identify any requirements for a tenant to continuously operate throughout the term. Furthermore, if a party desires any preferential options at a site, including an early termination right, a right of first refusal or option, or any expansion or contraction option, it is imperative that these rights are expressly set forth in the LOI.
In addition, an LOI should address any property-specific matter. If tenant improvements will be completed at the premises, the LOI should specify which party is completing the improvements, as well as any allowance that will be provided. In addition, an LOI should state verbatim the permitted use of the tenant. Further, when representing a retail tenant at a multitenant location, it is best practice for an LOI to include a copy of all exclusive uses and prohibited use restrictions currently in effect at the site so the tenant can identify any issues affecting its intended use of the premises.
Nonbinding Nature and Binding Exceptions
Most parties intend for LOIs to be nonbinding and simply a blueprint to future lease negotiations. However, a court may find an LOI to be enforceable, and, therefore, it is important that parties include certain nonbinding language in the letters. Specifically, LOIs should clearly state the letter is “nonbinding.” In addition, parties should include a statement in the LOI providing that the LOI should not be construed as a binding contract between the parties until a lease agreement is executed and delivered by both landlord and tenant.
In order to clarify the nonbinding nature of an LOI, counsel should remove any covenant for the parties to negotiate in good faith that may be included in a form LOI. Further, counsel should confirm that there is no characterization of an LOI as a final agreement in the letter.
Notwithstanding the general intent for LOIs to be nonbinding, parties may want to have certain provisions within an LOI to be binding upon execution of the letter. For example, when lease negotiations need to remain confidential, an LOI should include a confidentiality provision that is immediately binding on the parties. Also, if a tenant desires to restrict a landlord from marketing the property during lease negotiations, this “exclusivity” restriction should be binding on the parties upon execution of the LOI.
Conclusion
Despite their brevity, LOIs must be carefully drafted and negotiated and include all material terms for a proposed lease agreement so counsel can quickly proceed with legal negotiations in the most efficient manner.
The material in this publication was created as of the date set forth above and is based on laws, court decisions, administrative rulings and congressional materials that existed at that time, and should not be construed as legal advice or legal opinions on specific facts. The information in this publication is not intended to create, and the transmission and receipt of it does not constitute, a lawyer-client relationship.
Download the publications here.
In two recent decisions — Brown v. Teva Pharmaceuticals and Doe v. Valley Forge Military Academy & College — courts in the Eastern District of Pennsylvania put limits on the use of so-called “snap removal,” a strategy allowing in-state defendants to remove suits from state to federal court before being served with the state court summons and complaint. Now, defendants looking to win the removal race must file a notice of removal with both the federal and state court before being served, or risk losing access to a federal forum.
The Brown and Doe Decisions
The forum defendant rule, 28 U.S.C. § 1441(b)(2), prevents in-state defendants from removing suits to federal court solely on the basis of diversity jurisdiction. In 2018, the Third Circuit limited the rule’s scope, finding that the rule only takes effect once the in-state defendant has been “properly joined and served.” Encompass Ins. Co. v. Stone Mansion Rest. Inc., 902 F.3d 147 (3d Cir. 2018). In Pennsylvania, New Jersey and Delaware, in-state defendants may now remove state actions to federal court before service of process is completed. These “snap removals” provide in-state defendants access to a federal forum — as long as they act quickly and remove the case before being served.
The Encompass court, however, did not clarify the procedural steps necessary for snap removal to take effect. Removal has always been a multistep process: The defendant must file a notice of removal in federal court within 30 days of receiving the plaintiff’s initial pleading, 28 U.S.C. § 1446(b)(1), and it must also “promptly” provide notice of removal to all adverse parties and file a copy of the removal notice with the state court, 28 U.S.C. 1446(d). Given the necessary delay between filing a notice in federal court and filing a copy of the notice in state court, some defendants may notify the state court days after filing their notices of removal. This delay can be exacerbated when removing a case to a district court, such as the Eastern District of Pennsylvania, that requires notices of removal to be filed in person with the clerk’s office and not e-filed. Even though a notice of removal must be filed within 30 days of service, courts in the Third Circuit required only that the notice be filed with the state court “promptly” to properly effectuate removal. Indeed, Third Circuit courts have held that a copy of the notice of removal filed in state court a few days or even weeks after a timely federal court filing meets the procedural requirements of 28 U.S.C. § 1446. See Bajrami v. Reliance Standard Life Ins. Co., 334 F. Supp. 3d 659, 661 n.14 (E.D. Pa. 2018) (noting that in the Eastern District of Pennsylvania, “[c]ases have held that filing notice to the state court within a month after removal in federal court is deemed ‘prompt,’ as required by § 1446”).
But in the snap removal context, filing “promptly” with the state court may no longer suffice. In Brown and Doe, the district courts, faced with motions to remand, needed to determine whether the defendants perfected their snap removals when they filed their notices of removal in federal court before being served, but failed to file copies of this notice in the state court until after service occurred.
The defendants argued that the procedural requirements for snap removal were satisfied when the defendants “initiate[d] removal” by filing in federal court. Encompass, 902 F.3d at 153. The Brown and Doe courts, on the other hand, found that merely initiating removal before service is not enough. Removal must instead be “effected,” i.e., a defendant must (1) file its notice of removal in federal court, (2) notify adverse parties, and (3) file a copy of its notice of removal in state court, all before being served. Doe, 2019 U.S. Dist. LEXIS 117633, at *9-10. Accordingly, to take advantage of the snap removal exception to the forum defendant rule, Pennsylvania defendants must complete all of these procedural steps before service to win the removal race.
Implications of Doe and Brown in the Snap Removal Context and Beyond
The Brown and Doe holdings present a challenge for in-state defendants seeking removal on diversity grounds. While the act of filing a notice of removal with the federal court may be done with relative speed, the necessary delay between accomplishing the initial filing and providing a copy of this filing to the state court means that some defendants may be unable to take advantage of snap removal before being served. In-state defendants anticipating suit by out-of-state plaintiffs should be prepared to move quickly upon learning that a state court action has been filed if they wish to proceed in a federal forum.
Further, while it remains unclear what effect the Brown and Doe holdings may have outside the snap removal context, the opinions do offer an apt reminder that defendants should attempt to satisfy all procedural requirements of section 1446(d) within 30 days of service to avoid remand motions based on alleged untimeliness.
John L. Schweder II is a partner in the firm’s Trial and Dispute Resolution Practice Group, a seasoned and trial-ready team of advocates who help clients analyze and solve their most emergent and complex problems through negotiation, arbitration and litigation. Kaitlin L. O’Donnell and Brian H. Callaway are associates in the Trial and Dispute Resolution Practice Group.
The material in this publication was created as of the date set forth above and is based on laws, court decisions, administrative rulings and congressional materials that existed at that time, and should not be construed as legal advice or legal opinions on specific facts. The information in this publication is not intended to create, and the transmission and receipt of it does not constitute, a lawyer-client relationship.
This article is Chapter 3 in the Construction Law in the International Environment published by Almedina Publishing (Marcondes Editor) (2019). It is reprinted here with permission. It is available for purchase in Portuguese at https://www.almedina.com.br/9788584934911.
The goal of any construction project, no matter how large or small, is completion of the project on time, at or under budget, in conformance with the contract requirements, and to the satisfaction of the owner. Managing concurrent design, procurement, and construction activities becomes increasing complex as the size and duration of the project increases. Most large power, infrastructure, or energy projects require several to many years to construct, excluding the predecessor design and procurement activities. Large construction projects require the coordination of thousands of engineering, procurement and construction activities, and frequent schedule updates to strategically accommodate the myriad of changes that will occur in the design, procurement, and construction process.
This chapter focuses on the importance of appropriate project controls and proactive project management on large power, energy, and infrastructure construction projects (Megaprojects). The overall cost of each of these projects is into the billions of United States Dollars (USD), and the time to complete, from the earliest planning stages through project completion and close-out, will be lengthy, and could approach a decade. While certain design, procurement, and construction activities is often done concurrently to minimize the overall project delivery time, these projects nevertheless take a number of years to complete.
Project Delivery Systems and Risk Allocation
While not the primary focus of this chapter, there are many project delivery methodologies for Megaprojects, with the Engineering-Procurement-Construction (EPC or Turnkey) model (or a variant) being the most widely used. Each project delivery methodology has various advantages and disadvantages.1 Each contracting structure attempts to allocate risk among the parties, i.e., allocate the legal and financial consequences of cost and schedule uncertainty among the contracting parties, including schedule delay, unforeseen conditions, and any other type of situation that could affect project cost or schedule.
There are numerous causes of cost and schedule uncertainty on Megaprojects, some of which are global or “macro-level” in nature and some of which project specific risks, or “micro-level” in nature. Common macro-level risks that may present challenges on Megaprojects include availability and/or cost of capital, currency fluctuations, supply and/or wage inflation, political and regulatory influences, cultural dynamics, technological issues, availability and cost of skilled labor, availability and cost of skilled managers, and financial market forces. Common project specific construction risks include design or technology novelty or uniqueness, design complexity, market conditions leading to planned schedule acceleration,2 unforeseen, unexpected, or differing conditions, force majeure events, owner-directed changes, design completion, refinement or enhancement, contractor productivity issues, labor unrest, coordination of contractors and subcontractors, coordination of engineering with procurement and construction activities, skilled labor unavailability, design, procurement, or construction delays, financial wherewithal of contractor and major subcontractors and suppliers, local opposition to project, and other issues.3
It is virtually impossible to eliminate all exposure to macro and project level risks over the time duration of a Megaproject. Consequently, contractual risk allocation is of critical importance. Careful contract drafting attempts to allocate the legal consequences of these risks among the parties, and typically attempts to shift risk away from the owner/lender to other project participants.4 While risks can be allocated and exposure can be controlled to some extent through careful contract drafting, the minimization of project risk also requires appropriate project controls and proactive project management.
Proactive Project Management
Proactive project management is the practice of systematically attempting to preemptively identify and address project schedule and cost issues before they adversely impact the project. Proactive project management can minimize schedule and cost risks on any construction project, but its importance is magnified significantly on Megaprojects. The successful completion of a Megaproject may hinge on the owner’s ability to anticipate that a contractor is running behind schedule, over budget, or financially strapped, is experiencing conflicts with suppliers or subcontractors, or is struggling with other significant issues which, unless promptly addressed, will adversely affect the progress of the project.
In order to further explore these issues, this article will use, as an example, a Megaproject contracted on an EPC basis, and will outline the importance to the owner of establishing appropriate project controls at the outset of a project to monitor and report contract execution on a “real-time” basis.
In an EPC contract, the owner has a single point of contact for the project, a firm referred to as the “EPC Contractor.” This firm handles the design of the project, the procurement of all construction materials, equipment, and construction services, and provides for the ‘turnkey’ delivery of the facility for an agreed contract price.5 An EPC Contractor takes an active role in the design of the project, the selection of the major equipment, contracting with all of the suppliers and subcontractors, and the integration of the design and procurement schedule into the project construction schedule. This integration, in theory, produces an alignment of team members for optimal project performance.
In an EPC project, therefore, it is imperative that the owner set strict schedule (with liquidated damages) and payment milestones, as well as performance guarantees (with “make-good” obligations and liquidated damages if the facility does not meet explicit performance standards). EPC contracts generally cost more than the sum of its various segments because the owner pays a risk premium to the EPC Contractor in return for (a) a guaranteed maximum price or fixed price, (b) an established project completion date, (c) strict performance with the performance guarantees, and (d) the aforementioned bundling of the engineering, procurement, and construction segments (as well as testing and commissioning) with the single EPC Contractor.
While the EPC model typically provides the owner with a reasonable degree of cost certainty at the outset of the project, insulation from most disputes arising on the project, including intra-consortium disputes and disputes with equipment vendors and subcontractors, and a reduction in project duration, the owner and/or lender still may face significant consequences in the event of non-performance by the EPC Contractor. The owner has placed “all its eggs in one basket” by ceding control of the engineering, procurement, and construction of the project to a single contracting partner, the EPC Contractor. If that entity faces a default by one of its major subcontractors or suppliers, fails to complete the project, fails to meet minimum performance requirements, goes bankrupt, or otherwise is unable or unwilling to perform or perform satisfactorily, the project will not be completed on time, customer relationships will be jeopardized, and the economic benefits to be derived from the project may well be lost. Depending upon the level and type of bonding and other security provided by the EPC Contractor, the owner will have to address mounting financial losses as the costs to complete the work far exceed the contractually agreed price, and the time for completion marches forward. Therefore, it is important for the owner to establish appropriate project controls and proactively monitor the EPC Contractor to mitigate this risk and maximize the likelihood of satisfactory and timely project completion.
As part of its tender, this EPC Contractor typically submits the initial ‘baseline’ project schedule, containing thousands of activities to be completed on the project, to the owner for review and approval. Part of the project award involves the owner contractually agreeing to this ‘baseline’ schedule. Before addressing issues with this ‘baseline’ schedule and its effects on the project execution phase, it is helpful to understand the entire project life cycle and the role project controls play during each project phase.
The Project Life Cycle
The life cycle of Megaprojects generally consists of the following five phases:6
-
Strategic Planning and Project Development: Feasibility studies, strategic planning, and project development
-
Scope Definition: project definition and refinement of the project’s scope
-
Procurement: procuring or contracting for the project
-
Project Execution: performance and execution of the work by the EPC Contractor, including design, procurement, construction, start-up, commissioning; and commercial operation of the project, and
-
Project Closeout: Financial closeout of the project, including resolution of any claims between the owner and the EPC Contractor.
The owner’s project control process must provide the framework for effective and prudent project management during the life of the project. The owner should institute internal project controls to document and monitor each step in the project life cycle. While the EPC Contractor is hired to execute the project, the owner’s internal project control process begins during the Strategic Planning and Project Development stage, and is further refined during the Scope Definition stage and as the tenders are evaluated and awarded during the Procurement stage. The owners project controls process should be is established at the award of the tender and before the EPC Contractor begins the Project Execution stage. Beginning at that initial phase, the owner must document the need for the project, its regulatory and financial feasibility, and its overall plan and strategy for the procurement and execution of the project. This ongoing documentation and project management function, while tedious, will prove essential for proactive project management throughout the Project Execution phase, and will be necessary in evaluating any claims that may arise on the project, and in meeting its periodic reporting obligations to its lenders and/or senior management team.
Each phase of the project life cycle has its own unique set of key questions which need to be considered, and the answers to those questions should be documented. During the Strategic Planning and Project Development phase, the owner’s answers to the following questions are examples of the types of decisions which must be documented and supported:7
-
Have appropriate processes and approvals been established for the selection of technology, the initial scope, the budget and schedule development, and financing decisions?
-
What type of project delivery system is appropriate for this project? (As discussed above, we assume an EPC project for purposes here; discussions of other project delivery systems are outside the scope of this chapter)
-
Were reasonable alternatives for the project delivery system considered?
-
Have all regulatory requirements and considerations been addressed?
-
Have the appropriate internal and governmental approvals been addressed?
-
Has an appropriate internal project management team been selected? Is it prudent to retain outside expertise to assist the internal project management team (legal, project management, scheduling and project controls, engineering, auditing, risk management, document retention and other functions)?
The following are examples of considerations that should be addressed and documented during the Scope Definition and Procurement phases:8
-
Who are the key stakeholders for the project and have they been engaged regarding major project decisions?
-
Have competing technologies been adequately vetted for use in completing the project?
-
How were the project vendors and contractors selected? What criteria were used in the selection process? Are those the appropriate criteria for this project? Are these criteria defensible to later challenge? Was this criteria appropriately followed in all instances?
-
Have project risks been identified and reasonably allocated through the procurement and contracting strategy?
-
Has an auditing or other feedback loop been established? Has an adequate quality assurance and quality control strategy been implemented?
During the Project Execution and Project Closeout phases, the owners’ answers to the following questions are examples of the types of decisions that should be addressed and documented:9
-
Has an established project management strategy been implemented and how does it function? Is the owner’s staffing appropriate?
-
Has an adequate framework of project controls been established and how does it function? Do the cost and scheduling controls address the project’s needs? Does this system provide accurate and reliable data?
-
Have communication and reporting systems been established to allow executive management to make timely and informed decisions?
-
Are periodic reviews of the project controls and processes conducted? If so, how often? Are these reviews performed by an independent auditor or an in-house auditor?
-
Do the project controls allow early issue identification? If so, how?Are steps in place to assure compliance with applicable laws?
-
Do the project controls facilitate quality assurance and quality control compliance? How?
-
Has a process been established to document major project decisions, including change management (i.e., the process by which changes to the scope of the project are formally introduced, approved, and recorded)?
-
Is there an independent process in place to provide a continuous improvement loop on identified project issues? Is this process adequately documented?
Internal project controls must be designed to document the decision-making process and must identify risks to schedule, budget and other project specific criteria. In addition, they should be designed to include a feedback loop, so that issues with the project controls, or the types of data or reporting provided, are identified and addressed promptly during the project.
Integrating the Contract Documents with the Owner’s Project Control Processes
In drafting and negotiating the contract documents, and in particular the EPC contract, the owner must be mindful of its information needs for the project. During the Strategic Planning and Project Development, Scope Definition and Refinement, and Procurement phases of the project life cycle, most of the information and data that the owner needs to monitor, document, support, and report, including project scope, budget, schedule, the regulatory and financial requirements, staffing, and a myriad of other decisions and analyses, is within its control. Some of the needed information may be provided by the owner’s advisors and other professionals (such as legal, accounting, engineering, risk, and the like), while preliminary pricing information may be provided by engineers, contractors, and vendors. The owner gathers the information that it needs to make decisions, and documents that its decision-making processes are appropriate, and that its decision-making process is prudent.
As the tender is made and the EPC contract is executed, the Project Execution phase begins, and much of the detailed information that the owner needs to proactively manage the project is developed by the EPC Contractor. The owner should independently verify work progress, quantity and quality of materials installed, design maturation, contractor labor and equipment quantities, or any other objective and observable criteria essential for the project’s progress and, ultimately, its successful delivery. However, much of this type of information is developed by the EPC Contractor in the first instance, and supplied to the owner on a periodic basis as mandatory support for its payment applications.
It is important that the owner, through the contract documents, require the frequent submittal of such information from the EPC Contractor in a form that can be readily used in its project controls process. The process of integrating the information and submittal requirements of the contract documents with the owner’s project controls process is a critical function that is sometimes overlooked during the contract drafting process. In other words, the requirements of the contract documents must meet the structure of the owner’s project management and controls process.
Project Controls: the Project Execution Phase and the EPC Contractor
One of the goals of the owner’s project controls process in the EPC environment is to minimize the risk that project delivery will fail under the EPC Contractor’s stewardship. Project controls should allow the early identification of performance, budget, and schedule risks, and allow the owner to make prudent decisions in light of the issues identified. The level of detail and the definition of the owner’s project controls system and staff varies based on the size, location, complexity, contract type, and risk profile of the project. However, the owner’s project control process should be designed to timely identify and address issues as they develop.
On most large capital projects, the owner needs to perform the following functions during the Project Execution phase:
-
Report the costs to date and forecast the costs to completion
-
Monitor, verify, and document project status against various metrics, including budget, schedule and payments
-
Verify schedule status, including the schedule status of major engineering, procurement and construction activities
-
Monitor the progress and status of the major subcontractors
-
Monitor and perform change management, including design maturation, and
-
Internal and external reporting of project data.
EPC Contractors should typically be required to submit the following types of information on a monthly basis as preconditions to invoice approval and payment: (a) contract and payment status; (b) schedule status; (c) schedule progress; (d) quantities installed; (e) quantities stored; (f) work-in-progress; (g) periodic and cumulative project costs; (h) project progress and other project metrics; (i) submittal logs; (j) drawing logs; (k) status of pending changes; (l) status of requests for information; and (m) a myriad of other project metrics (determined on a project-by-project basis). This information is typically provided through a detailed monthly progress report and monthly submittal process as a precondition to payment. The key here, from the owner’s perspective, is to ensure that the contract provisions require the contractor to submit the quantity and quality of information that the owner needs in the form most useful to the owner. At a minimum, the information must meet the tracking and reporting needs of the owner and must be sufficient to allow the owner to verify the validity of the construction and schedule progress. The project control process should work on a nearly ‘real-time’ basis to allow the owner to proactively address any identified schedule or cost issues. Generally, the owner would implement, at a minimum, the following internal processes for information, reporting and project management purposes:
- Project cost and budget controls
- Schedule management
- Earned value or other progress management
- Change management, and
- Risk management.
Establishing the Owner’s Project Control Process
The project delivery method, size and complexity of the project, internal corporate requirements, regulatory review and/or approval, and the contractor’s execution strategy affect the structure of the project control processes implemented on a particular Megaproject. AACE International (AACE) has established recommended practices for developing a project controls plan.10 One of the initial steps is to establish an adequate Work Breakdown Structure (WBS), which separates the project scope into logical work tasks. The owner will also create an Organizational Breakdown Structure (OBS) identifying the individual managers and clearly defining their roles and responsibilities. The team should then integrate the WBS, OBS, budget and resources through control accounts relating directly to WBS components, which will form the basis for the project control system. A project communication plan, including meeting requirements and reporting structures, should also be developed.
These components of the project controls system are discussed in more detail below.
Cost Baseline
The cost estimate should be credible, well-documented, accurate, and comprehensive.11 Historical cost data from similar projects is a good starting point for a parametric cost estimate. In addition to the estimates typically performed at the design stage, it is recommended that a third party independent cost estimate be performed near design completion. Such an estimate should review the original estimate assumptions, as well as indicate areas of potential risks in the contractor’s bid. Care should also be taken in establishing the contingency and the management reserve for the project, which will be based on management’s assessment of risks that should take into consideration numerous factors including the duration of the project, the maturity of the design, familiarity with the project type, geographic location, and similar factors.
Baseline Schedule
The schedule is ultimately a communication tool through which the contractor communicates the planned sequence of construction and the status of the project. The owner and contractor typically agree to a “baseline schedule” contemporaneously with project award, and the agreed “baseline schedule” will form the basis for all commercial purposes, including measuring the project’s progress, accessing liquidated damages, delay or disruption claims, or any other commercial purpose.12 The baseline schedule represents a mutually agreed plan that must accurately model the planned prosecution of the work.
The development of the initial project schedule is the result of coordination of multiple departments within the EPC Contractor.13 As such, from the EPC Contractor’s perspective, it is imperative that this coordinated development process be documented, as a reference during schedule reviews and as a basis for later evaluating the impact of changes. The schedule basis should document the assumptions made in the schedule development process, the scope of work, the items included and excluded in the schedule, the execution strategy, the planning methodology and any issues or concerns.
From the owner’s perspective, the schedule review meetings prior to the establishment of the “baseline schedule” should be well documented. At a minimum, the minutes from the schedule review meetings should document the assumptions made in the schedule development process, the scope of work, the items included and excluded in the schedule, the execution strategy, and the planning methodology. The schedule review meeting minutes should also document the level of participation by each of the major vendors of the EPC Contractors, including all affiliated companies, and should specifically document the integration of design and procurement of major systems and equipment into the project schedule. While it is axiomatic the E (engineering) and P (procurement) come before C (construction), the importance of the integration of engineering and procurement activities into the baseline schedule is sometimes overlooked. In order to minimize schedule risk, the owner’s project controls process must closely monitor engineering and procurement activities, particularly long lead items and major equipment vendors.
Engineering and procurement of major equipment or other components should be reflected in the schedule baseline. The basis for the duration estimates for procurement items should be documented. The status of procurement activities should be verified and updated on a regular basis. Special care should be taken in this regard as the contractor may not have direct knowledge of the manufacturing status.
Good scheduling practices should be followed in creating the schedule baseline. These include eliminating activities without predecessors or successors, minimizing the use of constraints and minimizing activities with durations longer than the update period. Presence of open ended activities and constraints will compromise the accuracy of the schedule and create artificial float values. In some scheduling software, activities with no successors may automatically be shown as critical. Constraints may be needed in some cases. For example, a “start no earlier than” constraint is often used when the activity is not planned to be worked on until a later period. Also, activities with durations longer than the update period should be minimized. Determining the level of completion of an activity in progress is subjective and hence will introduce errors while updating the schedules. Making the activity durations shorter than the update period will minimize the number of activities in progress in any individual schedule update. However, this consideration should be balanced with the level of complexity of the schedule and its usefulness in managing the project.
The critical path should be reviewed to confirm that it makes logical sense. A review should identify the required logical ties (hard logic) on the critical path and the preferential logical ties (soft logic). Use of preferential logical ties to place any individual work item on the critical or near critical path should be analyzed and documented. The percentage of critical and near critical activities should also be reviewed. As a rule of thumb, if the percentage of critical or near critical path activities is higher than 20 percent, further review of the schedule logic is warranted.
The schedule should also be reviewed for constructability.14 The constructability review will include identification of means and methods or construction sequence that will result in unnecessarily increasing the cost of the project. Another aspect will be a review to confirm that any site restrictions including restrictions to access and work periods are incorporated in the project schedule.
Monthly Project Updates
The owner dictates by contract the schedule and cost information is to be submitted on a periodic basis, and the format of the information to be submitted. From an owner’s perspective, a high level of transparency is preferable. Timely submittal and review of periodic project updates (usually monthly) will minimize disagreements over project status. Providing timely and accurate reviews of contractor schedules is an integral part of proactive schedule management.15
The monthly schedule update submittals usually contains a narrative describing the changes made to the schedule along with an electronic copy of the schedule update database and printed reports. Both the schedule narrative and reports should enable the reviewer to accurately assess the project’s progress and the changes in the schedule. Typical information in a monthly schedule narrative include activities that were started or completed in the update period, status of major procurement items, identification and explanation of any critical or near critical delays in the update period, identification and explanation of changes to schedule logic or planned durations and any potential schedule concerns or issues.16
The project’s WBS should to be established such that the codes match with the payment application at a higher level. If the project is set up in this way, the progress percentage updates to cost loaded activities can be compared with the monthly payment applications to verify the accuracy of the updates.
There is often a tendency to revise the logic to accelerate the remaining activities in a schedule to recover any prior delays. Such schedule revisions need to be reviewed to ensure that these are practical and not just “wishful thinking.” The contract should specify that the monthly reports address any schedule logic revisions and the reasons for it in a separate section.
Whenever work is prosecuted out of sequence, the schedule is no longer accurately modeling the project. However, most projects do not follow the planned sequence. A contractor may perform activities out of sequence for various reasons, including mitigation of delays, resource considerations, slippage of predecessor activates, including engineering or procurement, or other changes in the planned sequence. Whatever the reason, it is essential that the schedule logic be revised to reflect the actual sequence followed in the field so that the schedule remains an accurate model of the project.
Owners should review the numerous scheduling options available in newer scheduling software. A schedule will forecast different completion dates based on different schedule settings, even if the underlying schedule status and logic are the same. For example, common software settings to incorporate out of sequence progress include “retained logic,” “progress override” and “actual dates,” each of which will calculate a different completion date for the project. The scheduling options used in each schedule update should be documented as part of the monthly update process, so that the schedules could be recreated for review using electronic copies of the schedule database.
In case of disputes or claims, the as-built dates are often relied upon to quantify the delays. In the absence of accurate as-built dates in the schedule, considerable resources and money will have to be spent in determining these dates for a forensic schedule analysis. Thus, care should also be taken in documenting the actual dates of an activity. The actual start date is typically not the date on which preparatory work was started on the activity, but rather should reflect the date on which substantial work was started. Similarly, actual finish date is typically when the activity was substantially completed so that the successor activity could start. If only minor tasks are remaining on an activity, it may be prudent to separate it out as a separate task that is not critical or to incorporate it into a project-wide punch-list activity, whose subtasks are tracked outside of the schedule.
Earned Value Management
The project control plan should identify the processes necessary to perform a performance assessment on a periodic basis.17 The goal is to identify variances, opportunities and risks in a timely manner. The earned value management system integrates the project information, including cost, schedule, resources and productivity, and communicates it to the project stakeholders. Heightened visibility of cost and schedule performance is the primary benefit of earned value reports. The earned value system also helps identify project trends and establish a reasonable estimate of project cost at completion. Its predictive value includes identification of areas with potential cost or schedule overruns and thus helps manage risks on the project. Even on fixed price contracts, an earned value system is recommended as it provides an early warning system on any significant potential project issues.
Risk Management
Risk management involves risk identification, assessment, analysis, mitigation and contingency planning.18 Risk identification is often best performed by the senior project staff and typically includes a short description of the risk and may include a quantification of the risk. Historical change order and claims data on similar projects is a good source for risk identification and/or quantification. While identifying the risks, it is preferable to be over inclusive by identifying reasonably probable potential risks. The risk identification should be performed keeping the goals of the business in mind. These may be project goals like cost or schedule or may include broader corporate or strategic goals.
Risk assessment involves establishing the relative importance of the risk item by identifying its probability of occurrence as well as its potential impact. This is best done in a group where the underlying assumptions could be critically examined. The significance of potential impacts may be tied to the project approval criteria and triggers for additional reviews or approvals.
Risk analysis involves a review and analysis of the identified risks. Various quantitative processes could be used for this, but the ultimate aim is to identify the risks that could be mitigated. Risk analysis also includes the categorization of risks based on common root causes and impacts and the relationships between risks. Contingency, both cost and schedule, is derived from the risk analysis.
Risk mitigation may involve various strategies including prevention, transfer, hedging or insurance, or even “rebaselining” of the project.19 Risk management plan should be a dynamic document that defines these processes and is refined as required. The foundation of the risk management plan is the contractual allocation of risk set forth in the contract documents.
Change Management
Failure to timely resolve and incorporate individual changes into the project schedule is a certain recipe for claims, as the effect of the interaction of a multitude of individual issues will become more difficult to resolve later in the project.20 The contract should define the processes for managing changes in scope, time and cost. The contract typically defines the notice requirements from the contractor as well as the timeframes for providing cost and schedule estimates. It should also define the timeframe for owner’s review of the proposed changes, the change approval process, and the dispute resolution process if the parties cannot agree on the change or its impact.
During project execution, changes should be identified early to minimize risk. The project control plan should also address the different types of changes as well as the approval process. Changes must be carefully evaluated, and after approval must be incorporated into the revised performance measurements.
The change order log should track all proposed change orders, whether approved or not. The cost and schedule impact of each proposed change order should be tracked separately, so that discrete impacts could be segregated and quantified to assist resolution. Documenting the identification of the change, any relevant discussions and segregating the cost and schedule impacts is also critical in case of claims.
Project Closeout
Project closeout is an often overlooked as a part of the project control process. At project closeout, the project staff should document the lessons learned, as well as collect as-built documentation including final as-built schedule, final change order log, final cost report, and all other applicable close-out information. The as-planned documentation should also be preserved, including budget, cost estimates, schedule baseline and assumptions. Performing this data collection and evaluating it will help improve the delivery of future projects.
Conclusion
A principal goal of the owner’s project control function on a Megaproject is to timely identify and address cost, schedule, and other performance issues as they develop. Given the EPC nature of this type of project (i.e., the owner only interacts with the EPC Contractor on the project), the need for the owner to remain informed on all aspects of the project’s progress is paramount. The contract documents should be drafted so that adequate reporting requirements are incorporated to meet the needs of the owner’s project control system. The contract documents should likewise reflect the risk management plan. The contract provisions for scheduling, schedule updates, earned values, project costs, and project progress must assist in managing project risks at the appropriate level by meeting the information, tracking and reporting needs of the owner.
Endnotes
1 “Project delivery system” means the manner in which an owner contracts for engineering, procurement, and construction services on a project. While there are many variants, three common delivery methods are the general contractor model, the EPC or Turnkey model, or a hybrid approach while divides the work into multiple contracts. See Bates, “Strategic Considerations in North American Megaprojects,” Managing Gigaprojects: Advice from Those Who’ve Been There and Done That (American Society of Civil Engineers 2012). See also “EPC Contracts in the Power Sector,” DLA Piper 2012.
2 In order to complete the project in the shortest available time, an owner may contract to have construction proceed on an accelerated basis, such as working 50 to 60 or more hours per work week, planned second shifts for all or significant portions of the project, increasing manpower above optimal levels, increased modularization, or other techniques. Due to the labor inefficiencies inherent with extended overtime, techniques such as these are typically implemented only if directed and paid for by the owner.
3 McGraw Hill Construction, working in conjunction with the American Institute of Architects Large Firm Roundtable and other industry partners, surveyed more than 1,500 owners, architects, and contactors to ascertain their perceptions on which factors lead to the greatest degree of uncertainty on construction projects. Their research identified the following as the top seven causes of uncertainty on construction projects: 1) implementation of an accelerated design and construction schedule; 2) changes made by the owner during design and construction; 3) design errors; 4) design omissions; 5) contractor and subcontractor coordination issues; 6) contractor-caused delays; and, 7) unforeseen site or construction conditions. See Managing Uncertainty and Expectations in Design and Construction,” SmartMarket Report (2014) (available at www.construction.com). Several other factors rated very low in this survey (identified by less than 7 percent of respondents), including project delivery system, project complexity, and regulatory permitting processes.
4 Owners/lenders typically attempt to contractually allocate all or substantially all of the project risks to the EPC Contractor in order to minimize their exposure to cost and schedule risk. See Bates, supra note 1, at 365 – 368.
5 Price certainty is typically required in order to obtain project financing. In other words, the project must be “bankable,” with the EPC Contractor usually bearing the risk of any cost overruns or schedule delays. The contract price may be a lump sum, a guaranteed maximum price (“GMP”), an initial “open-book period” that leads to the establishment of a fixed price, a GMP with shared “savings,” a GMP to be established based upon unit prices or agreed rates, or various other methods, but the contract must be bankable if external financing is involved. The method of arriving at the agreed contract price may be influenced by the nature of the project and the level of design completeness and/or owner requirements at the time of contracting, but the owner/lender will typically require contract price certainty with an appropriate contingency. For a more robust discussion of EPC pricing structures, see “EPC Contracts in the Power Sector,” infra at note 1; Lamberski, “EPC Agreement Pricing Issues in First of a Kind Power Plant Projects,” Construction Users Roundtable Voice (Fall 2012).
6 These stages may occur concurrently to some extent. For example, in the EPC context, the Scope Definition and Procurement phases may blur, as alternative technologies or other alternative means of accomplishing the owner’s objectives are considered. Similarly, an owner may procure turbines or other long lead supply items prior to finalization of a contract with an EPC Contractor, and assign all obligations under the supply contract to the EPC Contractor (sometimes called an “EPC-wrap”).
7 These are merely examples of the types of decisions that must be made, documented, and supported during the Strategic Planning and Project Development stage. This is not intended to be an exhaustive list of the issues faced during this stage.
8 These are merely examples of the types of decisions that must be made, documented, and supported during the Scope Definition and Procurement stages. This is not intended to be an exhaustive list of the issues faced during these phases.
9 These are merely examples of the types of decisions that must be made, documented, and supported during the Project Execution and Project Closeout stages. This is not intended to be an exhaustive list of the issues faced during these phases.
10 See generally Developing the Project Controls Plan, AACE International Recommended Practice No. 60R-10, December 21, 2011; Project Planning – As Applied in Engineering and Construction for Capital Projects, AACE International Recommended Practice No. 39R-06, December 8, 2011.
11 See generally Kul B. Uppal, Best Practice of Cost Estimates, AACE International Transactions, 2003.
12 The importance of agreeing to a “baseline schedule” at project award cannot be overstated. The “baseline schedule” is critical component of the commercial agreement, and is the foundation of delay and disruption claims, assessment of liquidated damages, and various other commercial undertakings. Nevertheless, all too often time is spent in arbitration or litigation attempting to establish which schedule should be used as the “baseline schedule” because the “baseline schedule” was not yet agreed at the time of award.
13 Various portions of the design, procurement, and construction schedules are typically developed by different project partners and must be integrated by the EPC Contractor. This is a major task that is critical for project execution. Gaining a meaningful understanding of the proposed schedule prior to award can be a daunting task for an owner. Nevertheless, the owner must develop an meaningful understanding of the EPC schedule in order to evaluate and agree to the project “baseline schedule.”
14 See generally Schedule Constructability Review, AACE International Recommended Practice No. 48R-06, August 28, 2009.
15 See generally Scheduling Claims Protection Methods, AACE International Recommended Practice No. 45R-08, June 1, 2009; Schedule Update Review – As Applied in Engineering, Procurement and Construction, AACE International Recommended Practice No. 53R-06, August 14, 2008.
16 Owner’s use a software utility such as “Claim Digger” to compare the electronic schedule update with the prior update to document month to month changes in schedule logic or activities. EPC Contractors are sometimes required to submit such an electronic comparison with schedule updates or with significant change order proposals.
17 See generally Joseph J. Orczyk, Progress Measurement and Earned Value, Skills and Knowledge of Cost Engineering 5th Ed., 2004, at 14.1; Robert A. Marshall, The Contribution of Earned Value Management to Project Success on Contracted Efforts, Journal of Contract Management, Summer 2007.
18 See generally Allen C. Hamilton, Risk Management, Skills and Knowledge of Cost Engineering 5th Ed., 2004, at 31.1; Eric Esperne, Translating Risk Management into Contract Management, Contract Management, Aug. 2010, at 56.
19 “Rebaselining” is the process of establishing a revised “baseline schedule” for a project during construction, typically as part of the resolution of a series of disputes. Essentially, as part of the consideration for resolving the dispute, the parties agree to a rebaselined schedule that will, from that date forward, govern their commercial relationship.
20 See generally Marlene M. Hyde, John P. Orr & Michael A. Peek, Best Practices by Owners for Controlling Cost and Schedules on Large Projects, AACE International Transactions (2010).
The author would like to thank Sunu M. Pillai, then a JD candidate at the University of Pittsburgh and now an associate in the Pittsburgh office of Saul Ewing LLP, for his invaluable research assistance in the preparation of this chapter.
Download the publication here
Imagine that your company has just commenced an internal compliance investigation in response to an allegation that the company is violating various federal laws. The next day, a longtime employee with access to the company’s crucial trade secrets is seen removing duffle bags of documents. Moreover, the IT department examines his network activity and reports that he has downloaded thousands of documents onto a thumb drive.
Shortly thereafter, an attorney for the employee contacts your litigation department and states that the employee has indeed taken documents and files with the company’s trade secrets. Further, the employee will not return the information because under the federal Defend Trade Secrets Act (DTSA), he is immune from liability under any federal or state trade secret laws because he has disclosed the company’s trade secrets “solely for the purpose of reporting or investigating a suspected violation of the law.”
Is the employee in fact immunized from liability for his acquisition and disclosure of your trade secrets? One might assume yes based on the DTSA’s whistleblower immunity provision, but the answer is actually more complicated and will depend on a number of factors. As further analyzed below, the whistleblower immunity provision is actually quite narrow and should be understood as a public policy-based exception within the context of the overall scheme of state and federal laws that prohibit misappropriating and disclosing trade secrets. Indeed, the few decisions addressing the immunity provision to date have declined to find immunity at a case’s early stages and have instead required the disclosing party (who seeks to rely on immunity) to establish each of the elements of the immunity through discovery, including, most notably, that the disclosure was, in fact, “solely for the purpose of reporting or investigating a suspected violation of the law.”
A second crucial question is whether the DTSA’s immunity provision prevents your company from taking steps to retrieve and protect the trade secrets that the employee has taken. Based on the DTSA’s language, and the few cases that have analyzed the immunity provision thus far, the answer to this question is a resounding “no.” Even in the context of legitimate whistleblowing activity, the law arms companies that have been the victims of trade secret theft with various tools to limit the possible harm caused by the misappropriation and to prevent further disclosure of the trade secrets. Below, we discuss these tools and certain strategies for using them that trade secret owners should employ to ensure that their trade secrets are not revealed to the public and/or their competitors.
The DTSA’s Protections for Trade Secrets
Enacted in 2016, the DTSA recognizes that trade secrets are a valuable form of intellectual property and, therefore, provides for criminal and civil penalties against those who misappropriate trade secrets.1 In private civil actions, a company that has been the victim of a trade secret misappropriation may ask the court to enter an order (called an injunction) that prevents any actual or threatened misappropriation, requires affirmative actions to prevent harm to the trade secret, and (in exceptional circumstances) requires payment of a royalty to the trade secret owner.2 The court may also award the trade secret owner money damages, exemplary damages and attorney fees.3 Finally, trade secret owners may, in extraordinary circumstances, apply to a court ex parte (i.e., without notifying the alleged perpetrator of the misappropriation) for an “order providing for the seizure of property necessary to prevent the propagation or dissemination of the trade secret that is the subject of the action.”4
The DTSA broadly identifies information that can qualify as a trade secret, provided that the information delivers a competitive advantage and the owner takes steps to protect it. The DTSA defines a “trade secret” as:
All forms and types of financial, business, scientific, technical, economic, or engineering information, including patterns, plans, compilations, program devices, formulas, designs, prototypes, methods, techniques, processes, procedures, programs, or codes, whether tangible or intangible, and whether or how stored, compiled, or memorialized physically, electronically, graphically, photographically, or in writing if:
(A) The owner thereof has taken reasonable measures to keep such information secret.
(B) The information derives independent economic value, actual or potential, from not being generally known to, and not being readily ascertainable through proper means by, another person who can obtain economic value from the disclosure or use of the information.5
The DTSA punishes the “misappropriation” of trade secrets, which it defines as follows:
(A) Acquisition of a trade secret of another by a person who knows or has reason to know that the trade secret was acquired by improper means –or–
(B) Disclosure or use of a trade secret of another without express or implied consent by a person who:
(i) Used improper means to acquire knowledge of the trade secret
(ii) At the time of disclosure or use, knew or had reason to know that the knowledge of the trade secret was
(I) Derived from or through a person who had used improper means to acquire the trade secret
(II) Acquired under circumstances giving rise to a duty to maintain the secrecy of the trade secret or limit the use of the trade secret –or–
(III) Derived from or through a person who owed a duty to the person seeking relief to maintain the secrecy of the trade secret or limit the use of the trade secret –or–
(iii) Before a material change of the position of the person, knew or had reason to know that
(I) The trade secret was a trade secret.
(II) Knowledge of the trade secret had been acquired by accident or mistake.6
In sum, the DTSA clearly describes both what secrets it protects (any nonpublic information from which a company derives competitive advantage, so long as the company takes steps to maintain the secrecy) and from what it protects those secrets (the improper theft or disclosure of that information).
The DTSA’s Immunity for Whistleblowers
During the final stages of the legislative process, the drafters of the DTSA added a provision that provides immunity to individuals who misappropriate trade secrets for the purpose of whistleblowing. The purpose of including this provision was “to ensure that employers and other entities cannot bully whistleblowers or other litigants by threatening them with a lawsuit for trade secret theft.”7 As Senator Leahy explained in support of the provision, it “protects disclosures made in confidence to law enforcement or an attorney for the purpose of reporting a suspected violation of law and disclosures made in the course of a lawsuit, provided that the disclosure is made under seal.”8
The immunity provision, titled “Immunity From Liability for Confidential Disclosure of a Trade Secret to the Government or in a Court Filing,” is strongly worded to convey the power of the whistleblower protection being afforded. It states:
(1) Immunity.—An individual shall not be held criminally or civilly liable under any Federal or State trade secret law for the disclosure of a trade secret that—
(A) is made—
(i) in confidence to a Federal, State, or local government official, either directly or indirectly, or to an attorney; and
(ii) solely for the purpose of reporting or investigating a suspected violation of law; or
(B) is made in a complaint or other document filed in a lawsuit or other proceeding, if such filing is made under seal.9
Moreover, an employee is expressly permitted to use trade secrets in an anti-retaliation lawsuit, provided that he or she “files any document containing the trade secret under seal; and . . . does not disclose the trade secret, except pursuant to court order.”10
Another notable feature of the DTSA is its notice requirement. This notice requirement arguably increases the odds of external whistleblowing activity because it requires employers to provide written notice of the immunity to employees “in any employee contract governing the use of trade secrets or other confidential information.”11 There are penalties for noncompliance with this notice requirement; an employer that fails to provide notice may not be awarded the exemplary damages or attorney fees that are available under the DTSA in an action against an employee to whom notice was not provided.12
Despite these strong protections for whistleblowers, the DTSA does set important limitations on the whistleblower’s conduct. For instance, the DTSA’s immunity provision expressly does not grant carte blanche permission for a person to violate other laws in securing trade secrets before disclosing them. Instead, the DTSA states that “[e]xcept as expressly provided for under this subsection, nothing in this subsection shall be construed to authorize, or limit liability for, an act that is otherwise prohibited by law, such as the unlawful access of material by unauthorized means.”13 Moreover, in the context of disclosures to government officials or an attorney, the disclosure must be “solely for the purpose of reporting or investigating a suspected violation of law.”14
When Whistleblowing May Involve the Disclosure of Trade Secrets
As explained above, trade secrets can cover a broad array of information, with examples including business methodologies, customer information, financial information, business and marketing plans, formulas (including algorithms), computer programs, personnel information, and pricing.
Unsurprisingly, a company’s trade secrets — i.e., its most secret and valuable information — can also serve as supporting evidence for a whistleblower action. By definition, a whistleblower is only entitled to recovery if he or she alleges violations of law that are otherwise unknown, i.e., that are based on nonpublic information. Depending on the conduct at issue, this nonpublic information may include trade secrets.
As a result of this nonpublic information requirement, the vast majority of whistleblower cases against companies are brought by former or current employees (i.e., “insiders”). Whistleblowers come in many shapes and forms, and there is no single explanation for why certain employees end up bringing allegations of wrongdoing to government prosecutors. Some individuals are motivated by the promise of a financial windfall — e.g., whistleblowers who disclose a company’s violations of the federal False Claims Act (in what are known as qui tam cases) are entitled to an award of up to one-third of any governmental recovery (which in many cases can be tens of millions of dollars). Other whistleblowers bring claims because they are upset with, or distrustful of the company — e.g., individuals who repeatedly raised allegations internally but were ignored or, worse, individuals who were terminated or demoted for raising complaints.
Regardless of the whistleblower’s motivation, though, the moment he or she contacts an attorney or provides information to a government prosecutor, the company loses the ability to control the situation, and the chances of a government investigation and/or interference increase exponentially.
Judicial Interpretations of the DTSA’s Whistleblower Provision
To date, there have been precious few judicial interpretations of the DTSA’s whistleblower provision, and, thus, the state of the jurisprudence on this topic remains very much in flux. However, two federal courts on opposite sides of the country — one in Massachusetts and the other in California — have provided some brief analysis of the substance of the provision. Although neither court dissected the immunity in detail, there are nonetheless important lessons that can be gleaned from these decisions.
The federal court in Massachusetts was the first court to address this provision in Unum Group v. Loftus.15 That case involved a lawsuit by a company in the business of providing financial protection benefits (Unum) against a former employee (Loftus) for stealing trade secrets. Specifically, Unum alleged that, after Loftus was interviewed by Unum’s in-house counsel as part of an internal investigation into its claims practices, Loftus removed boxes of confidential company documents from the premises. These documents, Unum alleged, contained trade secrets, such as “customer and employee information, and . . . protected health information.”16
Loftus moved to dismiss the Unum complaint on DTSA immunity grounds, claiming that he removed the documents for the purpose of reporting a violation of law by Unum. Specifically, Loftus claimed that he “handed Unum’s documents over to his attorney to pursue legal action against Unum for alleged unlawful activities.”17
The California case, 1-800 Remodel, Inc. v. Bodor,18 presented a similar fact pattern. That case was, once again, brought by a company (1-800 Remodel) against a former employee (Bodor) for theft of trade secrets. In this case, the company had investigated Bodor based on suspicion that she was overstating her hours. When Bodor learned of this investigation, she forwarded confidential documents to her personal email account and deleted many other files from her work computer. 1-800 Remodel terminated her and brought suit for theft of trade secrets. Bodor moved to dismiss, claiming that she was immune under the DTSA because she took the documents in order to report the company to the California Department of Consumer Affairs Contractors State License Board.
As discussed in more detail below, both of these federal courts ultimately denied the defendants’ motions to dismiss and allowed the employers’ suits for theft of trade secrets to proceed. In fact, to date, there has been only a single instance of a defendant succeeding even in part on a DTSA immunity claim, and that occurred in a Pennsylvania case that presented a unique and narrow set of circumstances. In Christian v. Lannett Co.,19 a terminated employee (Christian) brought discrimination charges against her former employer (Lannett). The DTSA immunity arose when Lannett asserted counterclaims that Christian had stolen and disclosed trade secrets in violation of the DTSA on two occasions. The first was Christian’s initial theft of 22,000 pages of confidential documents. This occurred before the DTSA was passed. The second was Christian’s disclosure of those same documents during the discovery phase of the litigation. This disclosure took place after the DTSA was passed.
The court determined that the DTSA did not, as a matter of law, apply to the initial alleged theft of trade secrets that predated its enactment. That left only the second, post-enactment disclosure during discovery and within the context of the employee’s discrimination lawsuit. The court ruled that the employee was immune from liability for this disclosure because it occurred within the context of a lawsuit.
How Trade Secret Owners Should Address the Whistleblower Immunity Provision
The DTSA’s immunity provision has real teeth. A whistleblower will almost certainly be immune from liability under federal and state trade secrets laws if he or she meets the provision’s requirements. Nonetheless, even in a potentially valid whistleblower situation, the DTSA does not seek to destroy the trade secrets, nor to prevent the trade secret owner from taking steps to protect the secrets during the pendency of the case.
First, it is important to understand that the immunity provision seeks to preserve the confidentiality of the trade secrets, even while recognizing that limited disclosures may occur during the whistleblower investigation process. To be eligible for immunity, the whistleblower must have made the disclosure in confidence to law enforcement authorities or an attorney. Similarly, if the disclosure is made in a complaint or other document, the filing must be made under seal. Thus, even the immunity provision recognizes the importance of strictly limiting a disclosure to only those who “need to know” for the purpose of conducting the whistleblower investigation.
Second, the provision itself, and the manner by which it has been interpreted so far, encourage a trade secret owner to move very quickly when it learns of a misappropriation. In both Unum and 1-800-Remodel, the trade secret owners got to the court first and filed civil complaints against the perpetrator employees for misappropriation. When the defendant employees asserted the immunity provision as affirmative defenses, both judges were dubious (at the pleadings stage) of whether the misappropriations were, in fact, exclusively linked to any whistleblowing activity.
This was largely because, when faced with the question of whether immunity applied, the judge in each case was constrained by the facts pled in the four corners of the complaint, i.e., the facts that the companies chose to include. In both cases, because the complaints were carefully pled by the companies, they did not contain sufficient allegations about the whistleblowing activity to permit the judge to rule that the defendants had met all of the necessary elements for immunity to apply. In contrast, the employee in Lannett got to the court before the company, filed her own claims for various violations of federal law, and succeeded in her immunity defense to the employer’s misappropriation counterclaim.
Third, the whistleblower immunity provision does not prevent a trade secret owner from using certain tools at its disposal, including requesting court orders/injunctions and seeking ex parte seizure of the trade secrets. In Unum, for instance, the court entered an order requiring the employee to take several steps to protect the secrets during the pendency of the case, including delivering to the court all documents he had taken, destroying all copies of all documents he had taken, and providing an affidavit stating the circumstances under which the employee had provided documents to any third party. Notably, the court ordered this relief despite knowing that the defendant may have a future need for the documents to prove his own case. The court noted that, in such an event, the defendant could seek the documents in discovery.
Fourth, the immunity provision protects a whistleblower from liability flowing from disclosure of trade secrets (provided that the disclosure complies with the statute), but does not protect the whistleblower from liability that may flow from the method by which he or she acquired the trade secrets. The statute explicitly recognizes this disclosure/acquisition dichotomy. The immunity provision states that “[e]xcept as expressly provided for under this subsection, nothing in this subsection shall be construed to authorize, or limit liability for, an act that is otherwise prohibited by law, such as the unlawful access of material by unauthorized means.”20
While this subsection has not yet been the subject of litigation, both Unum and 1-800-Remodel suggest that defendants may be liable for their acts in illegally acquiring trade secrets. In Unum, the court found that the company was likely to succeed on the merits of its conversion claim based on the employee’s taking of the documents without authorization and for refusing to return those documents. Similarly, in 1-800-Remodel, the company’s claim under the Computer Fraud and Abuse Act (CFAA) survived the employee’s motion to dismiss where the employee took a laptop without authorization and forwarded confidential and proprietary information to her personal email address. The court also questioned the applicability of the DTSA immunity to the CFAA claim because the employee did “not establish that the CFAA is a ‘trade secret law’ that is subject to [the DTSA immunity provision].”21
Fifth and finally, a trade secret owner should be prepared to aggressively test the purported whistleblower’s contention that he or she meets each and every one of the immunity provision’s elements. On its face, the provision will not apply unless (1) liability against the individual is sought under a federal or state “trade secret law”; (2) the individual disclosed the trade secret in confidence; (3) to a government official or an attorney; (4) for the sole purpose of making a report; (5) based on the individual’s suspicion that the law was broken. This will not be an easy task for an individual claiming immunity, especially at the motion to dismiss stage, where the decision is bound by the allegations the trade secret owner asserts in the complaint (as discussed above).
For example, on the basis of the four corners of the complaint, individuals seeking immunity will have a difficult time establishing that the disclosure of trade secrets was “solely for the purpose of reporting or investigating a suspected violation of the law.” In Unum, the court rejected the defendant’s immunity argument in part because, based on the record (i.e., the complaint filed by Unum), it was not clear “whether [Loftus] used, is using, or plans to use, those documents for any purpose other than investigating a potential violation of law.”22 Moreover, the Unum court likewise noted that Loftus had not filed a lawsuit against his employer based on the trade secrets at issue, and there was nothing reflecting the importance and contents of the documents he had taken.
The court’s analysis in 1-800 Remodel followed this same line of reasoning, but expanded it to other necessary elements for immunity as well. In rejecting the employee’s immunity claim, the court noted that the record (which, again, was composed only of the complaint drafted by the trade secret owner) did not “reveal the precise nature of the complaints Defendant threatened to — and later did — file . . . or whether the complaints she did file were made ‘in confidence.’”23
Conclusion
The DTSA’s immunity provision, including the notice requirement, may ultimately prove to both increase the likelihood of whistleblowing activity and embolden would-be whistleblowers through its grant of immunity. While trade secret owners must, of course, address the ramifications of the whistleblower activity, they must not lose sight of the fact that trade secrets are, by definition, a competitive advantage that can easily be lost through disclosure to the public and/or competitors. And trade secret owners should not be scared off from pursuing their rights as vigorously as possible by the DTSA’s immunity provision. In fact, the DTSA and the immunity provision make it even more critical than ever before for trade secret owners to act quickly and decisively to prevent their trade secrets from unnecessarily being held hostage, even during the whistleblower process.
Endnotes
1 18 U.S.C. §§ 1832, 1836.
2 18 U.S.C. § 1836(b)(3)(A).
3 18 U.S.C. § 1836(b)(3)(B) – (D).
4 18 U.S.C. § 1836(b)(2)(A)(i).
5 18 U.S.C. § 1839(3).
6 18 U.S.C. § 1839(5).
7 P. Menell, The Defend Trade Secrets Act Whistleblower Immunity Provision: A Legislative History, 1 Bus. Entrepreneurship & Tax. L. Rev. 398 (2017).
8 162 CONG. REC. S1636-37 (daily ed. Apr. 4, 2016).
9 18 U.S.C. § 1833 (emphasis added).
10 18 U.S.C. § 1833(b)(2).
11 18 U.S.C. § 1833(b)(3).
12 18 U.S.C. § 1833(b)(3)(C).
13 18 U.S.C. § 1833(b)(5) (emphasis added).
14 18 U.S.C. § 1833(b)(1)(A)(ii).
15 220 F. Supp. 3d 143 (D. Mass. 2016).
16 Id. at 146-147.
17 Id. at 147.
18 2018 U.S. Dist. LEXIS 2250000 (C.D. Cal. 2018).
19 2018 U.S. Dist. LEXIS 52793 (E.D. Pa. 2018).
20 18 U.S.C. § 1833(b)(5).
21 1-800 Remodel, 2018 U.S. Dist. LEXIS 2250000, at *18 n.9.
22 Unum, 220 F. Supp. 3d at 147.
23 1-800 Remodel, 2018 U.S. Dist. LEXIS 2250000, at *17.
William Taylor is a partner in the firm’s Trial and Dispute Resolution Practice Group, a seasoned and trial-ready team of advocates who help clients analyze and solve their most emergent and complex problems through negotiation, arbitration and litigation. Callan Stein is a partner in the Health Sciences Department, a team of 110 attorneys who collaborate across disciplines to solve complex legal challenges confronting clients throughout the health sciences spectrum.
The material in this publication was created as of the date set forth above and is based on laws, court decisions, administrative rulings and congressional materials that existed at that time, and should not be construed as legal advice or legal opinions on specific facts. The information in this publication is not intended to create, and the transmission and receipt of it does not constitute, a lawyer-client relationship.
This article was published in the August 1, 2019 edition of the Middle Market Growth Weekly newsletter, distributed by the Association for Corporate Growth (ACG).
Download the publication here.
On July 9, a final rule was adopted lifting the Volcker Rule’s restrictions on community banks from proprietary trading, and hedge funds and private equity funds from using the same name as an affiliated investment adviser, consistent with the Economic Growth, Regulatory Relief, and Consumer Protection Act (EGRRCPA).
The adoption of the final rule provides important guidance to hedge funds and private equity funds, including:
-
Certain community banks are excluded from the Volcker Rule, thereby allowing them to invest in private equity and hedge funds.
-
Hedge funds and private equity funds can now use the same name or a variation of the same name as an affiliated investment adviser, subject to certain exceptions.
Background
The Volcker Rule prohibits banks from using customer deposits for short-term proprietary trading of securities, derivatives and commodity futures, as well as options on any of these instruments. Banks cannot own, invest in or sponsor hedge funds, private equity funds or other trading operations (subject to certain exceptions). Banks can underwrite and offer hedge funds and private equity funds only if these activities do not create a material conflict of interest, expose the institution to high-risk assets or trading strategies, or generate instability within the bank or within the overall U.S. financial system. The Volcker Rule aims to discourage banks from taking too much risk by barring them from using their own funds to make these types of investments to increase profits. The Volcker Rule relies on the principle that these speculative trading activities do not benefit banks’ customers.
The Volcker Rule, in section 619 of the Dodd-Frank Wall Street Reform and Consumer Protection Act of 2010, was introduced in response to the 2007-2008 financial crisis. After the nation’s biggest banks accumulated large losses from their proprietary trading divisions, former Federal Reserve Chair Paul Volcker proposed regulations to reestablish the divide between commercial banking and investment banking, a separation that was extinguished by the Gramm-Leach-Bliley Act in 1999.
In December 2013, five federal agencies — the Board of Governors of the Federal Reserve System, the Federal Deposit Insurance Corporation, the Office of the Comptroller of the Currency, the Commodity Futures Trading Commission and the Securities and Exchange Commission — approved the final regulations that make up the Volcker Rule.
On May 24, 2018, President Trump signed the EGRRCPA in an effort to ease many of the regulations adopted after the passage of the Dodd-Frank Act, including the Volcker Rule. Shortly thereafter, on December 18, 2018, the agencies proposed a rule consistent with the EGRRCPA that would exclude certain community banks from the Volcker Rule, thereby allowing them to invest in private equity and hedge funds. On July 9, 2019, the agencies adopted the rule without change.
Analysis
Community banks up to a certain size are excluded from the Volcker Rule
The final rule excludes certain institutions from the definition of a “banking entity.” Previously, the definition included any insured depository institution, any company that controls an insured depository, or any bank holding company and any affiliate or subsidiary of such an entity. The final rule excludes from the Volcker Rule banks with:
-
$10 billion or less in total consolidated assets, and
-
total trading assets and liabilities that amount to 5 percent or less of their total consolidated assets.
As a result, a bank that meets this statutory exclusion is no longer considered a “banking entity” required to comply with the Volcker Rule.
Hedge funds and private equity funds can have the same name as their affiliated investment advisers under certain circumstances
The final rule also eased the Volcker Rule’s restrictions on affiliations between investment advisers and hedge funds or private equity funds. Investment advisers can have the same name or a variation of the same name as the hedge funds and private equity funds that they sponsor and in which they invest, subject to the following conditions:
-
the investment adviser is not an insured depository institution, a company that controls an insured depository institution, or a bank holding company
-
the investment adviser does not have the same name or a variation of the same name as an insured depository institution, a company that controls an insured depository institution, or a bank holding company
-
the name does not contain the work “bank.”
Takeaways
Community banks and other insured depository institutions that meet the criteria above are no longer subject to the Volcker Rule. While the long-term practical effects remain to be seen, the increased scope and flexibility in trading activities these entities now have will make them attractive partners in private equity funds and hedge funds, spurring financial activity and innovation.
Private equity funds and hedge funds are now able to have the same names and variations of names as the investment advisers that are their sponsors and investors under certain circumstances. This change allows funds whose investment advisers meet the criteria to gain potentially greater market visibility. Funds can now utilize the value of the affiliated investment adviser to more effectively market the fund. The size of this benefit is hard to quantify, as it depends on a number of factors specific to each fund, including business models, the overlap of fund marketing targets and banking entity customers, and customer reaction — but the potential benefits are large.
The material in this publication was created as of the date set forth above and is based on laws, court decisions, administrative rulings and congressional materials that existed at that time, and should not be construed as legal advice or legal opinions on specific facts. The information in this publication is not intended to create, and the transmission and receipt of it does not constitute, a lawyer-client relationship.





