When you are in the business of creating content, it’s crucial to know when licenses or permissions are required to use the intellectual property of others (such as copyright and trademarks). In this article, we explore what fair use entails, how clearance and permissions are key areas of risk management for content creators, and provide advice on avoiding infringement claims and practical steps to manage these issues in your content creation business.
Copyright
Copyright is a bundle of rights granted to the creators of original works, giving them exclusive control over how their work is used, reproduced, and distributed. This includes things like photographs, music, movies, art, and software. Copyright protects the expression of an idea, not the idea itself. In order to distribute, adapt, or otherwise use the copyright works of others (such as including music in a post or showing a painting in the background of a video), you must: (1) ensure the work is in the public domain; (2) use the work in a way that constitutes fair use; or (3) have the permission of the owner of the work.
Public Domain
Copyrights are typically granted for a specific period, and once that period ends, the work enters the public domain. Once a work enters the public domain, anyone can use it without permission. Determining whether a work is in the public domain can be challenging because copyright terms may be calculated differently based on when the work was created and where. In the section on clearance below, we include some tips for determining whether a work is in the public domain.
Fair Use
You may be tempted to use a popular song, meme, artwork, or image in your content and rely on fair use to do so without permission. Copyright law considers the following fair use factors: (1) the purpose and character of the use, i.e., whether commercial or nonprofit; (2) the nature of the copyrighted work; (3) the amount/substantiality used in relation to the work as a whole; and (4) the effect of the use on the potential value of the work.[1] Two recent cases illustrate how the principal of fair use has been applied in the social media and advertising context: In Griner v. King,the district court found Congressman Steve King liable for copyright infringement after using a popular meme on social media to solicit campaign contributions. The defendant appealed the damages, arguing it made fair use of the image. The circuit court disagreed, stating use of the image was purely commercial and intended to solicit donations, and therefore was not fair use. In Eight Mile Style LLC et al. v. LaFontaine Ford St. Clair Inc, Eminem’s music publisher filed suit against a Detroit Ford dealership alleging the dealership referenced Eminem’s song “Lose Yourself” in ads that ran on social media. Although the case has since been dropped, it is indicative of the risks of using songs without permission in social media posts.
Be aware there is no magic percentage of a work you can use that constitutes fair use, and that every case will be fact-specific. In our practice, we have seen investors, distributors, and advertising agencies require representations that all social media content of a creator be noninfringing. To be able to give such a representation, it is important to clear all of the copyrighted work and trademarks of others you plan to use in your content.
Trademarks
When creating content for an advertiser, or your own brand, there may be times when other brands appear in the content, such as in the background of a video or image. Use of another party’s trademark without permission, whether intentionally or inadvertently, may not automatically be considered infringement. Classic fair use under trademark law is an affirmative defense that requires the defendant to show the term is (1) not used as a trademark; (2) used only to describe the goods and/or services; and (3) used fairly and in good faith. For example, in the case of Solid 21, Inc. v. Breitling U.S.A., Inc., a watch manufacturer’s use of “red gold” in product advertisement was descriptive and did not infringe the plaintiff’s RED GOLD trademark for identical goods. It may also be acceptable to use another party’s trademarks in your content to describe their product or compare it to your product or one you are advertising; this is known as nominative fair use. Nominative fair use is use of another’s mark to identify the trademark owner’s goods and/or services. The use does not suggest sponsorship or endorsement by the trademark holder. However, if you do more than compare products and actually encourage the consumer to use both products together, this may suggest endorsement and lead to consumer confusion, which is not fair use. Simply having a product with a trademark visible in the background of a video may not be infringement, unless the product is that of a competitor of the company you are advertising for or you use the product in a way that disparages the goodwill of the trademark.
Avoiding Infringement: Clearance
The best way to avoid infringement claims when using third-party work is to clear the use of the work beforehand. This could include an assessment of whether the work is in the public domain or whether the use will be considered “fair.” Clearance may also take the form of searches of copyright and trademark registers and other public sources. For longer works, you may consider hiring a clearance firm that specializes in media clearances.
Copyright
The most useful resource to help determine whether a book, film, photograph, or song is in the public domain is the U.S. Copyright Public Catalog. The catalog contains a record of registered U.S. copyrights from 1978 to present and is a great starting point to locate information on the owner of works and copyright terms, among other information. Keep in mind, the U.S. Copyright Public Catalog only contains a record of registered copyrights, and a work not listed in the catalog may still be subject to copyright protection depending on the date of creation.
Trademarks
The two main sources to search for determining trademark ownership and rights are the U.S. Patent and Trademark Office, for registered marks, and the Internet, for uses of unregistered trademarks. When conducting Internet searches look for registered domains, websites where the trademark is used with goods and services in the U.S., and references to the trademarks in online publications to determine ownership.
Avoiding Infringement: Inadvertent Use
When creating content for commercial use, even an inadvertent inclusion of a trademark, artwork, or building[2] in the background of a photograph, reel, video, or post could give rise to legal issues. Taking a few minutes to clear your setting and to investigate any restrictions in public places will go a long way to reducing this risk. Using a checklist or having a policy for employees and contractors to follow for each post is an effective way to ensure these mistakes don’t occur.
Negotiating Permissions and Licenses
If you determine that you will need a license to use someone’s work or trademark, you can reach out to the owner directly (particularly in the case of trademarks), publisher, or producer. Alternatively, there are organizations that can assist with these types of requests. For example, Shutterstock and Getty Images provide royalty-free licenses for editorial and stock images. In the case of music, there are many organizations that manage licensing, such as: ASCAP (American Society of Composers, Authors and Publishers), a performing rights organization (PRO) that collects royalties on behalf of songwriters and publishers; Harry Fox Agency: A U.S.-based music rights agency for reproduction rights; and Global Music Rights: A PRO that collects royalties for music performed online and through digital media. This is not an exhaustive list but a good starting point.
When negotiating licenses, be sure to have clarity on how the work may be used, how many times, what portions (if not all), any restrictions, credit requirements, and fees. Keep copies of all licenses.
Best Practices
Based on our experience working with content creators in a wide spectrum of media, here are five tips to help avoid intellectual property infringement claims:
-
Build clearance into your content creation process.
-
Review content for common issues before posting (products with trademarks in the background, music, clips from shows, artwork, or protected buildings).
-
Have a policy and procedure for you and your employees/contractors to follow.
-
Know what you have licensed and how you can use it.
-
When in doubt, seek legal advice.
[1] 17 U.S.C. § 107
[2] Many famous landmarks restrict photographer for commercial use.
Construction Partners Zach Torres-Fowler and Albee Bates were among the co-authors for the Mealey’s® International Arbitration Report article, “International Arbitration Experts Discuss the Efficiency of Artificial Intelligence Tools in International Arbitration.”
On June 23, the Treasury Department (Treasury) and the Internal Revenue Service (IRS) issued Notice 2025-31. This notice includes lists of information that taxpayers may use to determine whether they meet certain requirements for energy communities under the Statistical Area Category or the Coal Closure Category, each as described in Notice 2023-29, Notice 2023-45, Notice 2023-47, Notice 2024-30, and Notice 2024-48.
Notice 2023-29 provides rules for determining what constitutes an energy community, organized in three categories (the Brownfield Category, Statistical Area Category, and the Coal Closure Category). We described each of these in our previous alert on Notice 2023-29. Treasury and the IRS intend to include these rules in forthcoming proposed regulations concerning energy communities. The regulations will apply to taxable years ending after April 4, 2023. Until the issuance of the proposed regulations, taxpayers may rely on Notice 2023-29, Notice 2023-45, Notice 2023-47, Notice 2024-30, Notice 2024-48, and Notice 2025-31.
Notice 2025-31
Notice 2025-31 provides five new appendices that taxpayers may use to determine whether they meet certain requirements under the Statistical Area Category or the Coal Closure Category, each as described below.
- The appendices in Notice 2025-31, as well as the previous appendices published with Notices 2023-39, 2023-45, 2023-47, 2024-30, and Notice 2024-48 apply only to the energy community bonus applicable to the production tax credits and investment tax credits available under Sections 45, 45Y, 48, and 48E of the Code. They may not be used for purposes of the qualifying advanced manufacturing credit under Section 48C.
MSA and non-MSA Vintages
The Statistical Area Category includes each Metropolitan Statistical Area (MSA) and non-Metropolitan Statistical Area (non-MSA) that (1) has (or had at any time after December 31, 2009), 0.17% or greater direct employment (Fossil Fuel Employment) or 25% or greater local tax revenues (Fossil Fuel Tax Revenue) related to the extraction, processing, transport, or storage of coal, oil, or natural gas and (2) has an unemployment rate at or above the national average unemployment rate for the previous year, in each case as determined by the Secretary of the Treasury.
Appendices 1, 2, and 3 contain two “vintages” of delineations of MSAs and non-MSAs used for determination of Statistical Area Category eligibility. Vintage 1 reflects groupings of county and county-equivalents into MSAs and non-MSAs generally based on the 2010 Decennial Census, which were included in Appendix A to Notice 2023-29 and used for determination of Statistical Area Category eligibility in Notice 2023-29, Notice 2023-45, Notice 2023-47, Notice 2024-30, and Notice 2024-48. Vintage 2 reflects groupings of county and county-equivalents into MSAs and non-MSAs generally based on the 2020 Decennial Census.
- Counties may have changed MSA or non-MSA, as applicable, between the two vintages. Notice 2025-31 provides that a county may qualify as an energy community if it meets the criteria for both Fossil Fuel Employment and the unemployment rate under the same vintage.
Appendix 1
Appendix 1 to Notice 2025-31 lists each county or county-equivalent as well as its MSA or non-MSA, as applicable, for both Vintage 1 and Vintage 2.
Appendix 2
Appendix B of Notice 2023-29 listed each Metropolitan Statistical Area (MSA) and non-Metropolitan Statistical Area (non-MSA) that meets the Fossil Fuel Employment requirement described in Notice 2023-29, based on calculations using the annual County Files of the County Business Patterns (CBP) published by the Census Bureau for years 2010 through 2020.
Appendix 2 to Notice 2025-31 is a list of additional counties that have met the Fossil Fuel Employment threshold when using the 2022 CBP data as part of Vintage 1, Vintage 2, or both.
Appendix 3
Appendix 3 to Notice 2025-31 is a list of MSAs and non-MSAs that qualify as energy communities under the Statistical Area Category because they meet the Fossil Fuel Employment threshold and have an unemployment rate at or above the national average unemployment rate for calendar year 2024. The list in Appendix 3 uses 2024 calendar year county unemployment rates released on April 18, 2025, by the Local Area Unemployment Statistics (LAUS) program of the Bureau of Labor Statistics (BLS). The energy community status of the MSAs and non-MSAs listed in Appendix 3 is applicable as of June 23, 2025, and will continue until Treasury and the IRS issue an updated list based on unemployment rates for calendar year 2025.
- The June 23 applicability date is consistent with Notice 2024-48, which indicated that Appendix 1 to Notice 2024-48 would apply for the period beginning on June 7, 2024, and ending with the subsequent annual release (which in turn would apply for the period beginning with such annual release).
- Appendix 3 addresses eligibility under both Vintage 1 and Vintage 2.
Appendix 4
The Coal Closure Category includes census tracts, and census tracts directly adjoining such census tracts, in which: (1) a coal mine has closed after December 31, 1999, or (2) a coal-fired electric generating unit has been retired after December 31, 2009. Appendix C to Notice 2023-29 provided a list of census tracts that satisfied the Coal Closure Category and was subsequently updated by Appendix 3 to Notice 2023-47 and Appendix 2 to Notice 2024-48.
Appendix 4 to Notice 2025-31 lists the newly identified census tracts with either a coal mine closure or a coal-fired electric generating unit retirement, and census tracts that directly adjoin the census tracts with coal closures, using the Mine Safety and Health Administration’s (MSHA) Mine Data Retrieval System data and the U.S. Energy Information Administration’s EIA Form 860 and EIA Form 860M data as of April 1, 2025, and historical extracts from the MSHA’s Mine Data Retrieval System that enumerate each status change for a mine. Appendix 4 to Notice 2025-31 should be combined with Appendix C to Notice 2023-29, Appendix 3 to Notice 2023-47, and Appendix 2 to Notice 2024-48 to provide the full list of census tracts satisfying the Coal Closure Category.
Appendix 5
Appendix 5 to Notice 2025-31 lists those tracts contained in Appendix 4 that newly qualify for the Coal Closure Category because of location data corrections issued since the publication of Notice 2024-48. Notice 2025-31 provides that projects placed in service after 2022 that were outside an energy community and are located in a census tract listed in Appendix 5 are eligible to claim the energy community bonus for taxable years starting after 2022.
- Notice 2024-48 did not include a comparable list to Appendix 5 that distinguished newly identified census tracts according to whether the additions (in Appendix 2 to Notice 2024-48) were the result of mines closing or generating units retiring since December 31, 2022, or were the result of updates to location information since the publication of the previous appendices. In our alert on Notice 2024-48, we made that observation and noted Question 10 of “Timing and Location” Frequently Asked Questions for Energy Communities (FAQs) published on June 7 can be read to suggest that if a mine in a census tract closes in 2024 (and is listed in Appendix 2 to Notice 2024-48), the census tract would be treated as an energy community beginning in 2023. The addition of Appendix 5 in Notice 2025-31 could be read to imply that if a mine in a census tract closes in 2025 (and is listed in Appendix 4 to Notice 2025-31 but not Appendix 5 to Notice 2025-31), the census tract would not be treated as an energy community in 2023 or 2024.
Conclusion
Taxpayers have been eagerly awaiting the updated Statistical Area Category Appendix following the release of the calendar year 2024 unemployment data in April. Notice 2025-31 should provide certainty for developers and financing parties regarding projects whose qualification depends on their locations being included in the appropriate IRS appendix on the placed-in-service date. In addition, because sponsors can secure future energy community status by beginning construction on a project during a period in which it is located in an energy community, the release of Notice 2025-31 should allow developers to begin physical work or satisfy the 5% safe harbor with respect to projects located in MSAs and non-MSAs currently included on Appendix 3 of Notice 2025-31.
This article was originally published on June 25, 2025 on Legaltech News (LTN) and is republished here with permission.
Millions of companies use the Microsoft 365 suite of tools every day to create, communicate, and collaborate, but far fewer have adequately grappled with the legal risks introduced by Copilot, the powerful generative AI assistant embedded in those same applications. While Copilot can enhance employee productivity, creativity, and connectivity, it may do so at the expense of privacy, security, and compliance without adequate planning and oversight. In this article, I will first identify the potential pitfalls of a laissez-faire approach to deploying Copilot and then provide actionable recommendations on how to navigate those hazards.
One key distinction to make at the outset is between the consumer-facing version of Microsoft Copilot and the commercial-facing version known as Microsoft 365 Copilot. To add to the complexity, the consumer and commercial flavors of Copilot each have both free and paid tiers. Because Microsoft’s enterprise data protection controls and commitments apply only to the commercial iteration of Copilot, companies should take steps to ensure that authorized users are directed exclusively to that version of the standalone Copilot chatbot in the ordinary course, and the balance of this article will focus on the commercial Copilot offering.
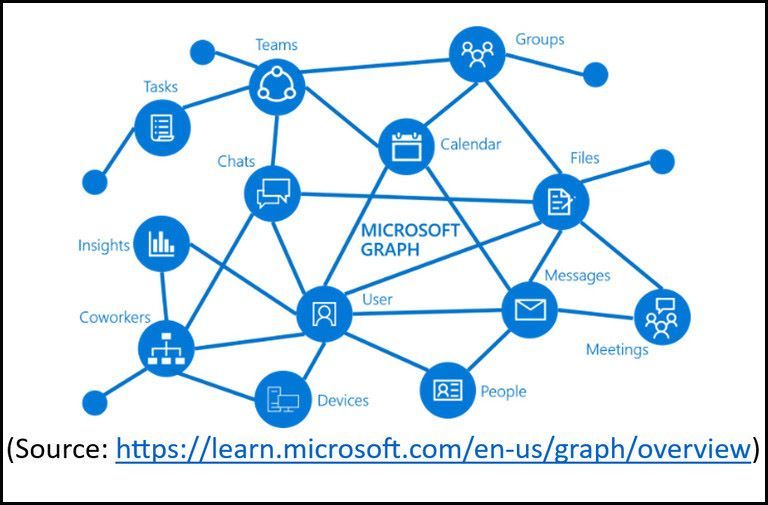
When composing its responses, Copilot leverages the incredible reach of the Microsoft Graph to reference the litany of emails, documents, Teams chats, meeting transcripts, and other data repositories that each user has permission to access within (and sometimes beyond) the Microsoft 365 ecosystem. But since many organizations rely more on “security by obscurity” than on a true “zero trust” or “least-privilege” approach to access controls, Copilot could surface sensitive content that a user technically always had permission to view if they knew where to look but would never otherwise have had reason to stumble upon. Microsoft has provided repeated assurances that the prompts, responses, and data accessed through Microsoft Graph are not used to train the foundation LLMs used by Copilot, but the risks of oversharing within the Copilot user base remain very real.
The tendency of many organizations to hoard information also means that Copilot is likely to encounter vast quantities of redundant, obsolete, and trivial (ROT) data as it traverses the Microsoft Graph, with no reliable way to set the ROT aside in favor of sources that are more reliable, accurate and useful. Just as a junior attorney might select an outmoded sample from a disorganized document management system when tasked with preparing their first memorandum, the quality of Copilot’s output can suffer as it struggles to separate the wheat from the chaff. In fact, Copilot could theoretically contribute to the problem by generating the very content that it then encounters when responding to future user prompts. This side effect of poor data hygiene is a variant on the phenomenon more broadly known as model collapse, wherein generative AI models trained primarily on their predecessors’ output produce increasingly inferior results.
Given its prodigious attack surface, Copilot has become an attractive target for threat actors. On June 11, 2025, cybersecurity researchers disclosed a zero-day vulnerability—since dubbed EchoLeak and already patched by Microsoft—that could bypass security controls and trick Copilot into exfiltrating sensitive corporate data simply by sending a benign-looking email with embedded prompt instructions that are executed during subsequent, seemingly-unrelated Copilot conversations. Frighteningly, this particular exploit did not depend on the recipient of the nefarious email clicking a link or taking any other action we all are assiduously trained to avoid.
The good news is that, with some effort and thoughtful planning, organizations can mitigate many of these risks without remaining on the Copilot sidelines. Microsoft Purview provides companies with the tools necessary to implement sound data classification, organization, and retention practices, including a labeling taxonomy that restricts Copilot’s access to sensitive data, but retroactively applying governance to terabytes of preexisting SharePoint site content may be daunting. Enabling Restricted SharePoint Search can be an effective stopgap measure by restricting Copilot’s scope of collaborative location coverage to an allowed list of curated SharePoint sites. Relatedly, while corporations have understandably sought to restrict the sprawl of repositories that SharePoint and Teams can unleash, imposing too many barriers on new site creation can lead users to commingle disparate information in a handful of preapproved locations, which can be equally problematic. Striking the right balance between structure and flexibility is critical.
As soon as Copilot is turned on, early adopters are bound to use it extensively, while others may proceed more warily. But companies need not take a “one-size-fits-all” approach to their Copilot deployment strategy. A phased rollout may be more prudent, perhaps starting with a small number of tech-savvy pilot participants, then expanding to those business functions likely to see the greatest productivity benefit at the lowest risk (e.g., sales and marketing), and eventually enabling teams who regularly handle the most sensitive data (e.g., human resources and legal) only after the governance model has been validated.
Once the floodgates are open, Copilot is virtually guaranteed to generate a steady stream of artifacts, much of which is likely to be discoverable (although precedent is still scant). The best time to enable reasonable data lifecycle management policies is before a user base grows accustomed to infinite retention. Absent a legal duty to preserve, the optimal duration to keep prompts, responses, document versions, meeting recaps, and other Copilot interactions will vary by organization and sometimes even by department, but adopting Microsoft’s generous out-of-the-box retention periods should be an explicit decision, not a dereliction.
Recognizing the challenges confronting organizations, Microsoft recently announced Copilot Control System, billed as a robust, coherent system of integrated enterprise-grade controls for Copilot and its agents covering security, governance, management, measurement, and reporting. But even with Microsoft’s assistance, companies should consider engaging experts to help assess their Copilot technical readiness; comply with international data protection regimes; avoid a damaging implementation misconfiguration; update applicable policies and procedures (including as to record retention, responsible AI use, and incident response), prepare and deliver real-world training; and assemble and advise cross-functional AI Centers of Excellence.
A Chapter 11 bankruptcy is often called “reorganization bankruptcy” and is typically used to preserve and maximize the going concern value of the debtor’s business. The life cycle of a Chapter 11 bankruptcy case can be conceptualized in five stages. Part I of this series focused on the first three stages.
This article will focus on the middle and final stages of a Chapter 11 proceeding, why it is important for stakeholders to understand these stages, and how their rights and financial interests can be affected. To access this article and read other insights from our Creditor’s Rights Toolkit, please click here.
State attorneys general increasingly impact businesses in all industries. Our nationally recognized state AG team has been trusted by clients for more than 20 years to navigate their most complicated state AG investigations and enforcement actions.
State Attorneys General Monitor analyzes regulatory actions by state AGs and other state administrative agencies throughout the nation. Contributors to this newsletter and related blog include attorneys experienced in regulatory enforcement, litigation, and compliance. Also visit our State Attorneys General Monitor microsite.
Contact our State AG Team at StateAG@troutman.com.
Troutman Pepper Locke Spotlight
American Bar Association’s State and Local Government Law Section Webinar Series: State Attorneys General Enforcement Actions and Litigation: The Unwritten Rules
By
Join Troutman Pepper Locke attorney Ashley Taylor, the co-leader of the firm’s State Attorneys General team, as he participates in part two of the American Bar Association’s State and Local Government Law Section webinar series titled “State Attorneys General Enforcement Actions and Litigation: The Unwritten Rules.” This session will focus on the “Multistate Investigations and Settlements” chapter from the recently published book, Consumer Protection: Understanding Enforcement Actions Brought by State Attorneys General. The webinar aims to delve into the complexities and nuances of enforcement actions initiated by consumer protection staff within state attorneys general offices.
Solicitors General Insights: The Legal Frontlines in Iowa and Indiana
By
In this episode of our special Regulatory Oversight: Solicitors General Insights series, Jeff Johnson is joined by Iowa Solicitor General Eric Wessan and Indiana Solicitor General James Barta to discuss their roles and responsibilities, as well as the current legal challenges their offices are facing. The conversation delves into the intricacies of state and federal court appeals, highlighting the significant amount of work done in state courts.
State AG News
Federal “Temporary Pause” of State AI Laws Clears Procedural Hurdle as Sides Draw Battle Lines
By
One of many provisions in the “One Big Beautiful Bill Act,” passed by the U.S. House of Representatives, would place a 10-year “temporary pause” on states’ ability to regulate artificial intelligence (AI). Initially called a moratorium, Senate Republicans changed the characterization of the prohibition to ensure the provision’s passage during the reconciliation process. The changes were at least partially successful, as the proposed “temporary pause” overcame a procedural hurdle when the Senate parliamentarian concluded that it satisfies the “Byrd Rule” and may remain in the bill. The bill now heads to the Senate floor. If enacted, the temporary pause would mark the most significant federal action (or inaction) related to AI.
Virginia Democratic Attorney General Primary: A Narrow Victory for Jay Jones
By
In a closely contested Democratic primary held on Tuesday, June 17, Virginia state delegate Jay Jones narrowly defeated Henrico County Commonwealth’s Attorney Shannon Taylor in the race for attorney general. This outcome sets the stage for a November election against Republican incumbent Jason Miyares, who advanced unopposed from his primary.
Court of Appeals Blocks Texas AG From Enforcing Pre-Litigation Subpoena
By
The U.S. Court of Appeals for the District of Columbia recently enjoined Texas Attorney General (AG) Ken Paxton from enforcing a pre-litigation subpoena issued to Media Matters for America (Media Matters). The subpoena is related to the Texas AG’s investigation into Media Matters arising out of allegations that the company fraudulently manipulated data after it reported about brand advertisement concerns on X.
FTC and Nevada AG Accuse ILM of Deceptive Advertising
By
Nevada Attorney General (AG) Aaron D. Ford recently announced that the State of Nevada and the Federal Trade Commission (FTC) have filed a suit against IYOVIA. IYOVIA currently operates under the brand names IM Mastery Academy, iMarketsLive, and IM Academy (collectively, “IML”) and is accused of falsely promising significant income through trading in various financial markets and through a multi-level marketing scheme.
AG of the Week
Todd Rokita, Indiana
Todd Rokita was elected Indiana’s 44thattorney general (AG) on November 3, 2020, earning the highest number of votes of any state officeholder in Indiana history. He was reelected in 2024.
During his tenure, Rokita established the Prosecution Assistance Unit to support local prosecutors in pursuing complex criminal cases. Under his leadership, more than 300 years of jail time have been handed down in financial fraud prosecutions — an Indiana record.
Before becoming AG, Rokita worked as general counsel and vice president of external affairs at Apex Benefits. He continues to serve as a director or advisory board member for several national and Indiana-based companies.
From 2011 to 2019, Rokita represented Indiana’s 4thcongressional district in the U.S. House of Representatives. He served as vice chairman of the House Budget Committee and chaired a subcommittee on the Education and the Workforce Committees.
Rokita previously served two terms as Indiana secretary of state from 2002 to 2010, and was elected president of the National Association of Secretaries of State. In this role, he supported the implementation and legal defense of the state’s photo voter ID law, which was upheld by the U.S. Supreme Court.
A Munster native, Rokita earned his undergraduate degree from Wabash College and his law degree from Indiana University’s Robert H. McKinney School of Law. He practiced privately before entering public service.
Indiana AG in the News:
- On June 16, Rokita provided new guidance to Indiana sheriffs on their obligations under Indiana’s anti-sanctuary law.
- On June 5, Rokita announced that he, alongside seven other state AGs, secured a court ruling permanently barring a robocall scammer from operating in the telecommunications industry.
- Rokita is encouraging consumers to take advantage of opportunities to return, fix, dispose, or replace a purchased recalled item.
Upcoming AG Events
- July: RAGA | Victory Fund Golf Retreat | Pebble Beach, CA
- July: DAGA | Presidential Partners Retreat | Santa Fe, NM
For more on upcoming AG Events, click here.
In Part One of this FAQ series, we break down Virginia’s Senate Bill 754, Consumer Protection Act; prohibited practices, etc., reproductive or sexual health information (Act), which amends the Virginia Consumer Protection Act (VCPA). The law goes into effect on July 1. Overall, given the broad definitions used in the Act, the law likely regulates organizations that are not traditional health care companies, and goes beyond traditional health information.
Part One focuses on the scope, applicability, and fines and penalties available to the Virginia attorney general (AG) and private litigants. We also explore the Act’s relationship to Virginia’s Consumer Data Protection Act (the VCDPA). Part Two of this series will analyze the requirements of the Act and how to comply.
What is the law’s purpose?
The Act is designed to protect reproductive and sexual health information (RHSI) by limiting certain data processing activities without the consent of the data subjects. The Act prohibits obtaining, disclosing, selling, or disseminating personally identifiable reproductive sexual health information without the consent of the consumer.
When does the law go into effect?
The Act goes into effect on July 1, and unlike other state privacy and AI laws, there is no stated grace period for enforcement.
To which organizations does this law apply?
The law applies to “suppliers,” which means any seller, lessor, licensor, or professional that advertises, solicits, or engages in consumer transactions. It also includes manufacturers, distributors, or licensors that advertise and sell, lease, or license foods or services to be resold, leased, or sublicensed by other persons in consumer transactions. A “consumer transaction” is the advertisement, sale, lease, license, or offering for sale, lease, or license, of goods or services.
Our take: While ostensibly a privacy law, the Act does not link into the VCDPA. As such, it does not include the applicability thresholds of the VCDPA (e.g., processing the personal data of 100,000 or more consumers during the calendar year), and small and nonprofits will be subject to the Act.
Does this law amend or impact the VCDPA? To which information does the law apply?
The Act regulates “reproductive or sexual health information,” defined as “information relating to the past, present, or future reproductive or sexual health of an individual.” The law provides a list of information falling into that definition (it does not indicate whether the list is exclusive):
-
Efforts to research or obtain reproductive health information services or supplies, including location information that may indicate whether an individual attempted to obtain services or supplies.
-
Reproductive or sexual health conditions or status.
-
Information about reproductive and sexual health-related surgeries and procedures.
-
Use or purchase of contraceptives, birth control, or other medication related to reproductive health.
-
Bodily functions or vital signs and other measurements.
-
Information about diagnoses, treatment, or medications.
-
Any of the above information that is derived or extrapolated from non-health-related information (such as proxy, derivative, inferred, emergent, or algorithmic data).
Our take:
Interestingly, the Act arguably defines reproductive or sexual health information broader than the definition of “personal data” under the VCDPA:
“Personal data” means any information that is linked or reasonably linkable to an identified or identifiable natural person. “Personal data” does not include de-identified data or publicly available information.
To qualify as RHSI, the information at issue must only ‘relate’ to the reproductive health of an individual. Unlike the definition of ‘personal data’ under the VCDPA, there is no explicit carve-out for de-identified or publicly available information. Additionally, the Act does not differentiate between “controllers” and “processors,” which means that vendors processing RHSI on behalf of other organizations are directly subject to the Act and must obtain consent for processing RHSI.
What are some examples of non-health care organizations that may be regulated under the act?
Like Washington’s MyHealthMyData law, given the potential breadth of this definition, organizations that don’t consider themselves health care companies or don’t believe they have reproductive health information, are likely to get swept into this regulatory scheme. Examples of companies that may get swept into the Act include:
-
Retailers. One of the more infamous privacy anecdotes involving information that could be considered RHSI related to Target and their apparent us of retail information to predict (and advertise about) a teenager’s pregnancy status. Data concerning purchases that enable a retailer to derive or extrapolate RHSI from non-health-related information (such as proxy, derivative, inferred, emergent, or algorithmic data) are within the scope of the Act.
-
Search engines. The Act regulates information concerning “efforts to research or obtain reproductive health information services or supplies,” which means search engines are likely within scope, as would be any organization that sells goods or services related to RHSI (e.g., drug stores) where information is captured concerning the obtaining of reproductive health information services or supplies.
-
On prem video. A video feed showing a person in a drug store buying a pregnancy test could constitute “information relating to the past, present, or future reproductive or sexual health of an individual.” Certainly, any video or other information related to reproductive health clinics (to the extent not regulated under the federal Health Insurance Portability and Accountability Act of 1996 (HIPAA)) may fall into the RHSI definition.
-
Online advertising-related data. Like the Target example, data in the targeted/behavior advertising space, even if non-health related information, appears to constitute RHSI if it can be used to extrapolate RHSI.
-
Past, present, or future “sexual health” of an individual. Sexual health could encompass a wide range of conditions affecting physical, emotional, and social well-being related to sexuality. These may include reproductive health issues such as erectile dysfunction, hormonal imbalances, psychological factors like anxiety or trauma, and the side effects of certain medications or chronic diseases.
-
Geolocation data. Geolocation data that can tie an individual to their attempt to obtain reproductive health information services or supplies may also pull in non-health care companies. Mapping services, connected vehicles, device companies utilizing geolocation data that track visitors to birthing centers, adoption facilities, abortion clinics, women’s health clinics, and other places where reproductive or sexual health services or supplies, may all be within scope of the Act.
Does the law include any exemptions?
Reproductive or sexual health information does not include health information that is protected under the HIPAA, or health records, or patient-identifying records used for certain purposes. However, since the Act amends and is made part of the VCPA, certain exemptions in the VDCPA will not apply, including entity-level exemptions for financial institutions and data-level exemptions for data regulated by laws like the FCRA and FERPA.
What happens if there is a violation of the law?
Violations of the VCPA are enforceable by the AG of Virginia, and may result in civil penalties of between $2,500 and $5,000 per violation.
Significantly, the VCPA (which was amended by the Act) provides consumers with a private right of action and the recovery of actual damages or $500 per violation (whichever is greater). Willful violations can result in the greater of three times actual damages or $1000 per violation. A successful plaintiff may also be awarded reasonable attorneys’ fees and court costs. Notably, the VCDPA does not provide for a private right of action, but does allow AGs to obtain penalties of up to $7,500 per violation.
On June 17, the Environmental Protection Agency (EPA) published a proposed rule to approve Texas’s application for primary permitting and enforcement responsibility (primacy) for carbon dioxide (CO2) sequestration wells pursuant to the Safe Drinking Water Act’s (SDWA) Class VI Underground Injection Control (UIC) Program. Upon approval of the rule, the Railroad Commission of Texas (RRC) will have permitting and enforcement authority for the Class VI UIC program (with oversight from the EPA). This development is the culmination of lengthy negotiations between the state of Texas and the EPA, which we have previously discussed in more detail.
It is widely expected that EPA’s delegation of the Class VI UIC program to the RRC will increase the speed and efficiency of permit issuance for carbon capture, utilization, and storage (CCUS) projects within the state. To date, CCUS projects have been bottlenecked by the slow pace of approvals at the EPA, with 62 projects currently under review and only 11 final permits having been issued. Permit applications in other states that have obtained primacy, such as North Dakota and Wyoming, have moved significantly faster than those subject to processing by EPA, and we expect the same result in Texas.
While primacy for the Class VI program has been anticipated for several years, another obstacle to CCUS projects in Texas has also been recently removed. On May 16, the Supreme Court of Texas issued a decision in Myers-Woodward, LLC v. Underground Services Markham, LLC,[1] holding that pore space below the surface belongs to the surface estate owner rather than the mineral estate owner. This decision provided much-needed clarity on a key legal issue relating to the underground storage of CO2: who owns the interstitial space in which injected gas is actually stored? Prior to Myers-Woodward, pore space ownership had been decided largely in favor of surface owners, but a 1991 case, Mapco, Inc. v. Carter[2] raised questions as to whether the mineral interest owner had a right to the empty space left behind after mining salt. Myers-Woodward explicitly overrules Mapco on that point, stating that empty, or “pore,” space belongs to the owner of the surface. As a result, prospective storers of carbon dioxide (and natural gas, for that matter) need only contract with the surface estate owner to secure rights to the pore spaces necessary to conduct storage operations.
With primacy imminent and pore space ownership clear, the remaining challenge for Texas carbon capture and storage projects is uncertainty surrounding transferability of the 45Q tax credit under the One Big Beautiful Bill Act (OBBB Act). CCUS projects qualify for tax credits available under Section 45Q of the Internal Revenue Code for the sequestration or utilization of qualified carbon oxides — carbon dioxide or other carbon oxides captured from an industrial source or by direct air capture. Currently, those credits may be transferred to unrelated taxpayers, but the version of the OBBB Act that passed the House of Representatives proposes to remove that transferability[3] for any CCUS equipment which begins construction two or more years after enactment of the OBBB Act. If the OBBB Act passes in its current form, the repeal of transferability will limit the availability of financing for potential CCUS projects. This ticking timer on credit transferability makes Texas’s imminent primacy even more important, as developers looking to retain the flexibility of the credit transfer may be racing against the clock to apply for and obtain their Class VI permits from the RRC in time to begin construction before the transferability deadline.
At Troutman Pepper Locke, we have extensive experience working with the Railroad Commission’s UIC department, with significant permitting and compliance representation relating to underground natural gas and helium storage facilities. We have also assisted with the preparation and submission of a Class VI permit application, as well as the commercialization of carbon capture and sequestration facilities. Our team is well-equipped to assist clients in navigating the complexities of Class VI well permitting, compliance, tax credit, and commercial issues.
For more information on how these changes may impact your projects or to discuss potential opportunities, please do not hesitate to contact the Troutman Pepper Locke team.
[1] — S.W.3d —, No. 22-0878, 2025 WL 1415892 (Tex. May 16, 2025).
[2] 808 S.W.2d 262, 274 (Tex. App.—Beaumont), rev’d in part on other grounds, 817 S.W.2d 686 (Tex. 1991).
[3] See section 112011 of the OBBB Act.
This article was republished in the January-February 2026 issue of The Journal of Robotics, Artificial Intelligence & Law.
On June 17, the U.S. Senate voted 68-30 to pass S.1582, the Guiding and Establishing National Innovation for U.S. Stablecoins Act, known as the GENIUS Act (the Act). This represents a landmark effort by the U.S. Congress to establish a comprehensive federal framework for the regulation of payment stablecoins. Passed with bipartisan support in the Senate, the Act aims to provide regulatory clarity, enhance consumer protection, and safeguard national security in the rapidly growing stablecoin sector.
Policy Objectives
The Act is designed to close regulatory gaps, mitigate systemic and illicit finance risks, and maintain the U.S. dollar’s dominance in the digital economy. It seeks to provide a clear legal pathway for stablecoin innovation while ensuring consumer and financial system protection.
Definition and Scope
Definition: The Act defines “payment stablecoins” as digital assets designed to maintain a stable value relative to a fixed amount of U.S. dollars or similarly liquid assets and intended for use as a means of payment or settlement. Only entities designated as “permitted payment stablecoin issuers” will be legally authorized to issue payment stablecoins in the U.S.
Permitted Payment Stablecoin Issuers: There are three categories of “permitted payment stablecoin issuers” in the U.S.:
- Subsidiaries of insured depository institutions (IDIs), subject to approval by the primary federal regulator of the IDI;
- Federal qualified payment stablecoin issuers, which include nonbank entities (other than a state qualified payment stablecoin issuer), OCC-chartered uninsured national banks, and federal branches that have been approved by the OCC; and
- State qualified payment stablecoin issuers, subject to approval by a “state payment stablecoin regulator.”
Permitted payment stablecoin issuers would be limited to the following activities:
- Issuing payment stablecoins;
- Redeeming payment stablecoins;
- Managing related reserves, including purchasing, selling, and holding reserve assets or providing custodial services for reserve assets;
- Providing custodial or safekeeping services for payment stablecoins, required reserves, or private keys of payment stablecoins;
- Undertaking other activities that directly support any of the permitted activities; and
- Other activities authorized by the primary federal or state regulator.
Permitted payment stablecoin issuers would be prohibited from paying interest to stablecoin holders.
Exclusivity: The Act makes it unlawful for any entity other than a permitted issuer to issue payment stablecoins in the U.S. The Act also makes it unlawful for a digital asset service provider to offer or sell a payment stablecoin to a person in the U.S. that is not issued by a permitted payment stablecoin issuer. Violations could result in fines of up to $1,000,000 per violation and up to five years of imprisonment.
Reserve and Redemption Requirements
Full Reserve Backing: Issuers must maintain reserves on at least a one-to-one basis with the value of outstanding stablecoins. Permitted reserves include:
- U.S. currency;
- U.S. Treasury bills, notes, or bonds with a remaining maturity of 93 days or less;
- Short-term repurchase and reverse repurchase agreements backed by Treasuries;
- Demand deposits or insured shares at IDIs; and
- Money market funds invested in any of the above assets.
Prohibition on Rehypothecation: Reserve assets cannot be pledged, rehypothecated, or reused, except for limited liquidity management purposes, and only with regulatory approval.
Reporting Requirements: Issuers must publish monthly disclosures of reserve composition, including the total number of outstanding stablecoins and the amount and type of reserves. Issuers with over $50 billion in market capitalization must also provide annual audited financial statements and disclose related party transactions and make them publicly available. Issuers must have their reserve information examined monthly by a registered public accounting firm, with executive officers certifying the accuracy of these reports. False certifications carry penalties.
Redemption Rights: Issuers must establish clear redemption procedures and publicly disclose their redemption policy, including all fees associated with purchasing or redeeming the payment stablecoins. All stablecoin holders have the legal right to redeem their coins at par value directly with the issuer.
Bankruptcy Proceedings
The Act amends the Bankruptcy Code to exclude required payment stablecoin reserves from the property of the debtor’s estate. Nonetheless, the Act’s Bankruptcy Code amendments refer to stablecoin holders’ redemption rights as “claims” in the bankruptcy, and expressly makes the automatic stay under 11 U.S.C. § 362 applicable to the reserves. Holders’ redemption claims are given superpriority status over all other claims in the case, both against the reserves themselves and — to the extent of any deficiency in the reserves — all other assets of the issuer. However, the Act’s amendments to the Bankruptcy Code make no provision for the payment of the costs of reconciling holders’ redemption claims or administering the reserves, raising questions about how an issuer bankruptcy would actually be viable.
Regulatory Oversight and Licensing
Federal and State Roles: Issuers with over $10 billion in market capitalization are subject to federal oversight from the Federal Reserve, Office of the Comptroller of the Currency (OCC), Federal Deposit Insurance Corporation (FDIC), or National Credit Union Administration (NCUA), depending on the issuer type, and these federal payment stablecoin regulators would have one year after enactment to promulgate regulations to carry out the Act through appropriate notice and comment rulemaking, including regulations implementing:
- Capital requirements;
- Liquidity standards;
- Reserve asset diversification; and
- Operational, compliance, and information technology risk management principles-based requirements and standards.
State qualified payment stablecoin issuers of not more than $10 billion would be allowed to choose state-level regulation if the state regime is “substantially similar” to federal standards. However, state qualified payment stablecoin issuers with more than $10 billion of outstanding issuance would be required to transition to the federal regulatory framework (to be administered jointly by the state and federal regulators), and state qualified payment stablecoin issuers that are state-chartered depository institutions would be subject to oversight by the primary federal payment stablecoin regulator of the state-chartered depository institution, while all other state qualified payment stablecoin issuers would be subject to oversight by the state and the OCC. States will be required to certify and recertify their regimes to the Treasury, and if the state regime is not certified or found insufficient, the issuer must transition to federal oversight within 360 days or stop issuing new stablecoins.
Licensing Regime: Subsidiaries of IDIs, certain uninsured banks, and approved non-bank entities will be able to issue stablecoins, and they will be subject to prudential standards similar to those for banks, including capital, liquidity, and risk management requirements.
Supervisory Authority: Federal and state regulators will have broad powers to license, regulate, supervise, examine, and enforce compliance, including the ability to suspend or revoke licenses, issue cease-and-desist orders, and impose penalties. Regulators may also remove institution-affiliated parties for violations and seek judicial enforcement of orders.
Consumer Protection
Marketing Restrictions: Issuers are prohibited from marketing stablecoins as “legal tender,” “U.S. government-backed,” or “FDIC insured.” Misrepresentation is subject to civil penalties up to $500,000 per violation.
Operational Limits: Issuers are restricted from using reserve assets for purposes other than backing the stablecoin and are generally barred from engaging in high-risk financial activities, such as proprietary trading or lending with reserves.
Prohibition on Payment of Interest: Issuers are prohibited from paying any form of interest or yield to holders of payment stablecoins solely in connection with the holding, use, or retention of such payment stablecoin.
Custodial Services: IDIs are permitted to provide custodial services for payment stablecoins, private keys of payment stablecoins, or reserves backing payment stablecoins. Federal banking agencies, the NCUA, and the Securities and Exchange Commission (SEC) are prohibited from requiring financial entities to report custodial digital assets as liabilities.
Custodian Requirements: Custodians are required to maintain asset segregation and are prohibited from commingling customer property with custodial property, with limited exceptions. Custodian requirements shall not apply to any person solely on the basis that such person engages in the business of providing hardware or software to facilitate a customer’s self-custody of their payment stablecoins or private keys.
Anti-Money Laundering (AML) and National Security
AML Compliance: Permitted payment stablecoin issuers are treated as financial institutions under the Bank Secrecy Act and all federal laws applicable to financial institutions in the U.S. relating to economic sanctions, the prevention of money laundering, customer identification, and due diligence. Issuers must implement AML and economic sanctions compliance as well as customer identification programs including verification (Know Your Customer) and appropriate enhanced due diligence, monitor and report suspicious transactions, and comply with recordkeeping and risk assessment requirements.
Technical Enforcement: Issuers must demonstrate the technical capability to comply with lawful orders, including the ability to freeze, block, or burn stablecoins as directed by courts or federal agencies. When feasible, the Treasury Secretary must coordinate with issuers before blocking transactions involving foreign entities.
Foreign Issuers: Foreign issuers may only issue payment stablecoins in the U.S. if they are from jurisdictions with comparable regulatory regimes, register with the Comptroller, and comply with U.S. lawful orders. Non-compliant foreign issuers are barred from U.S. markets, and the Treasury is authorized to take action if foreign stablecoin activity threatens financial integrity.
Enforcement Mechanisms
Civil and Criminal Penalties: Unlicensed issuance of stablecoins is subject to civil penalties of up to $100,000 per day, and criminal penalties of up to $1,000,000 per violation and five years of imprisonment. Licensed issuers and their affiliates face similar penalties for material violations and are subject to additional penalties for knowing or willful violations.
Cease-and-Desist Powers: Federal regulators can issue cease-and-desist orders, impose temporary suspensions, and seek judicial enforcement to address violations or protect customer interests.
Judicial Review: Aggrieved parties are entitled to judicial review of regulatory actions, ensuring due process and the right to appeal enforcement decisions.
What’s Next?
The Act represents a significant shift in U.S. financial regulation, introducing a tightly regulated environment for stablecoins, paving the way for more widespread, mainstream adoption of payment stablecoins by the general public. By mandating full reserve backing, robust oversight, and strong consumer and national security protections, the Act aims to foster innovation while still safeguarding the integrity of the U.S. financial system.
Next, the Act will go before the House of Representatives. It is expected that a conference committee, comprised of members of both chambers, will be formed to reconcile the GENIUS Act with the House’s similar, but not identical, Stablecoin Transparency and Accountability for a Better Ledger Economy (STABLE) Act. Once the committee is able to reconcile the differences between the two bills in a manner that is acceptable to both chambers of Congress, they will draft a conference report containing the agreed-upon text of the bill, which will require separate approval by the House and Senate. If both chambers approve the conference report, the final bill will be sent to the President for signature.
While there’s no definitive consensus, economists are closely monitoring the possibility of entering a recession this year. Economists agree a recession is not imminent, but caution the odds of facing a recession are higher than usual, and it’s important to understand recessions are declared months after significant economic slowdown, when two consecutive quarters of decreased gross domestic product (GDP) are recorded. Last quarter, the U.S. GDP decreased for the first time in three years. At worst, this indicates the beginning of a recession, and, at best, an economic slowdown.
Historically, patent case filings increase during economic slowdowns and recessions. In particular, a decrease in the GDP, like the one last quarter, is an economic indicator correlated with significant increases in patent litigation. Companies who choose to “double down” on their patents during economic slowdowns may emerge stronger than their competitors. On the other side, companies that anticipate being subject to patent disputes should prepare now to minimize risk and potential harm.
Agile companies understand that identifying alternative revenue streams and opportunities for growth, such as leveraging intellectual property assets, are key to navigating economic slowdowns. Economic slowdowns typically trigger patent asset divestments by operating companies because they are experiencing financial distress or because they are looking for new revenue streams amid the difficult economy. Many of these divestments often occur to litigation-prone licensing entities, which may increase the overall number of patent litigations. On the other hand, companies with valuable patent assets may choose to enforce their patents in venues such as the International Trade Commission, where powerful remedies like exclusion orders and cease-and-desist orders can protect their domestic revenue by ensuring their U.S. market share is not depleted by infringing imports. A strong patent portfolio and enforcement strategy may optimize long-term success during economic uncertainty.
For companies that have identified potential threats of patent litigation, steps can be taken now to better position themselves to mitigate risk and prevent significant financial setbacks.
Top Tips for Potential Plaintiffs
(1) Understand the scope of your intellectual property. Take inventory of your company’s patent(s), pending patent application(s), and information protected as trade secrets. Start building your knowledge of your company’s IP assets through discussions with your in-house counsel, engineers and technical experts, and intellectual property attorneys.
(2) Appreciate the varying beneficial outcomes available in asserting your patent. Evaluate your company’s goals to identify the most beneficial enforcement strategies. Offers to license, cease-and-desist letters, exclusion orders, injunctive relief, or money damages may all be considered when determining whether to bring suit and how.
(3) Consider alternative financing for litigation costs. During economic slowdowns, companies face a real concern when taking on new expenses related to litigation. However, this shouldn’t be a bar to planning enforcement strategies. Options may exist to support patent holders with funding and alternative or contingent fee arrangements. Consulting with an experienced litigation funding professional and setting realistic goals for litigation costs and outcomes may empower companies to enforce their patents at a reduced financial burden.
(4) Double-check your patents’ maintenance fees. All of the patents you plan to assert should be checked to ensure all fees are paid and that the patents did not expire from lapse in payment. Unintentional delay of fee payments can be rectified by submitting a petition for reinstatement with the overdue fees and applicable surcharges.
(5) Don’t assume infringement is not happening. Infringement can exist in numerous ways. It’s not limited to exact copying of your products; the pool of potential infringers is a lot larger than you might think. Often well-drafted patent claims are broader than the actual product that the patent application may have arisen from. This is where item #1 from above plays an important role. Companies should periodically revisit and review the scope of their patent claims as issued by the U.S. Patent and Trademark Office.
Top Tips for Potential Defendants
(1) Engage patent counsel. Immediately upon receiving notice of infringement, potentially by notice letter or by the initiation of an action, consult with experienced intellectual property attorneys who specialize in patent infringement. Early involvement of legal experts is essential to navigate the complexities of patent law effectively. Patent counsel can help devise a strong defensive strategy, discuss options for response, and provide a detailed analysis of the alleged claims and asserted patents. Better yet, retain and work with experienced patent litigation counsel even before any suit or threat of suit occurs to develop a response plan for early assessment and dispute resolution.
(2) Preserve and gather evidence. Proper documentation, including product design files, development records, communications, and any prior art relevant to the asserted patents, can be crucial in defending against infringement claims or challenging patent validity. If a suit has already been filed, time is of the essence to preserve documentation and get organized. Counsel can assist with litigation holds and evidence collection.
(3) Understand the threat and legal claims. If a suit has already been filed, carefully review the complaint to identify asserted patents, allegedly infringing products, designs, or functionalities, and other claims. If litigation is anticipated or actually threatened, consult with an attorney to assess the risk of infringement or other claims that may be anticipated, such as breach of contract claims or business torts.
(4) Evaluate your design and potential alternatives. Identify the key technical specialists or engineers on your team that could determine if there are noninfringing alternatives or design-around solutions to avoid anticipated claims of infringement. This proactive measure can mitigate potential infringement claim damages.
(5) Assess the impact to develop a strategy. Litigation can have far-reaching impacts. In addition to financial risk, litigation may impact operations or risk reputational harm. Identify your overall business objectives and values to appropriately consider strategic options to resolve the dispute, including settlement negotiations, licensing agreements, or proceeding to trial.
Isabella J. Profenno, a 2025 summer associate with Troutman Pepper Locke who is not admitted to practice law in any jurisdiction, also contributed to this article.





